https://tryhackme.com/room/webattackforensics-aoc2025-b4t7c1d5f8
Created by: tryhackme, strategos, marouane.elgorfte360
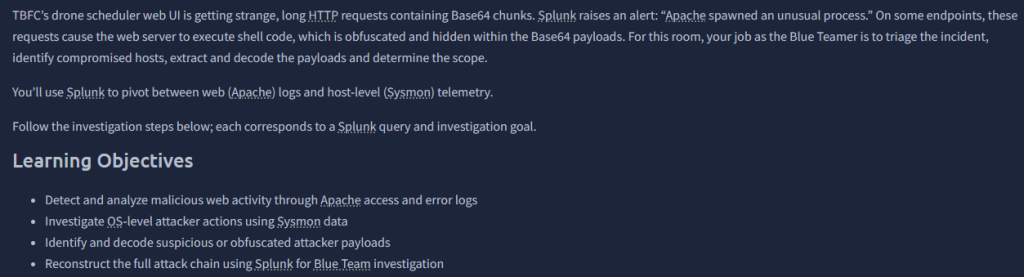
Per THM, “Splunk is a platform for collecting, storing, and analyzing machine data. It provides various tools for analyzing data, including search, correlation, and visualization. It is a powerful tool that organizations of all sizes can use to improve their IT operations and security posture.”
Before reading the material, go ahead and load both VMs. Once the attacker machine is loaded, launch Firefox and enter the address given to launch Splunk. Make sure you change your time range and keep an eye on it, or it will not populate results. At first, I tried 7 days, but nothing would populate, so best to keep it on “All time”.
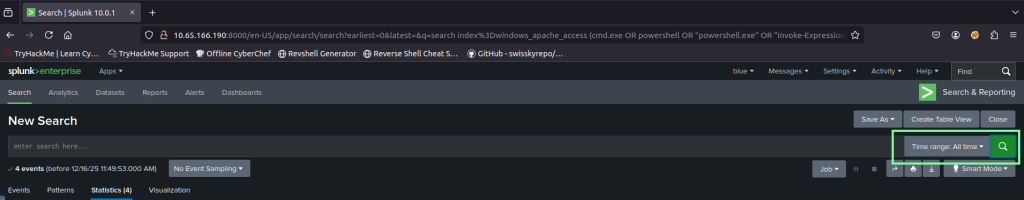
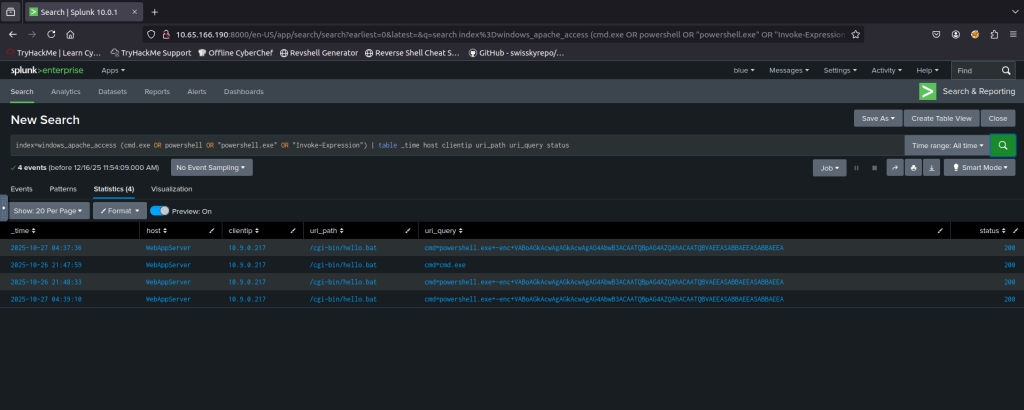
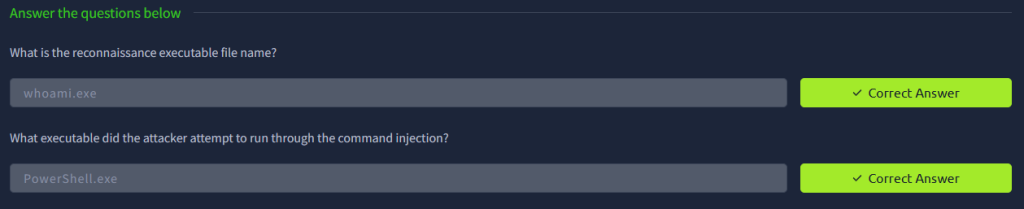
THM points out that these are signs of attempted command execution. We are tasked with copying and pasting the string linked to PowerShell.exe to this site: https://www.base64decode.org/ and decoding it. Doing so reveals the message: This is now Mine! MUAHAAHAA.
We are now tasked with looking at the web server error logs with a new query. The web server is Apache. Per THM, “Apache is the most widely used web server software. Developed and maintained by the Apache Software Foundation, Apache is an open source software available for free.” With this command, make sure to change it to the Raw format from the View dropdown. Again, we see the PowerShell.exe displayed.

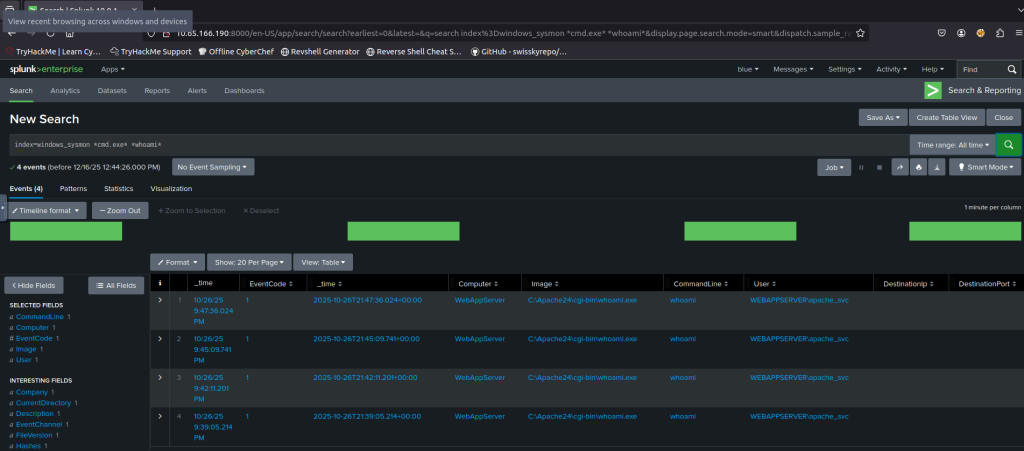
Next, we will look at Sysmon logs. Per THM, “Sysmon refers to System Monitor, which is a Windows system service and device driver developed by Microsoft that is designed to monitor and log various events happening within a Windows system.” Change the View: tab to View: Table.
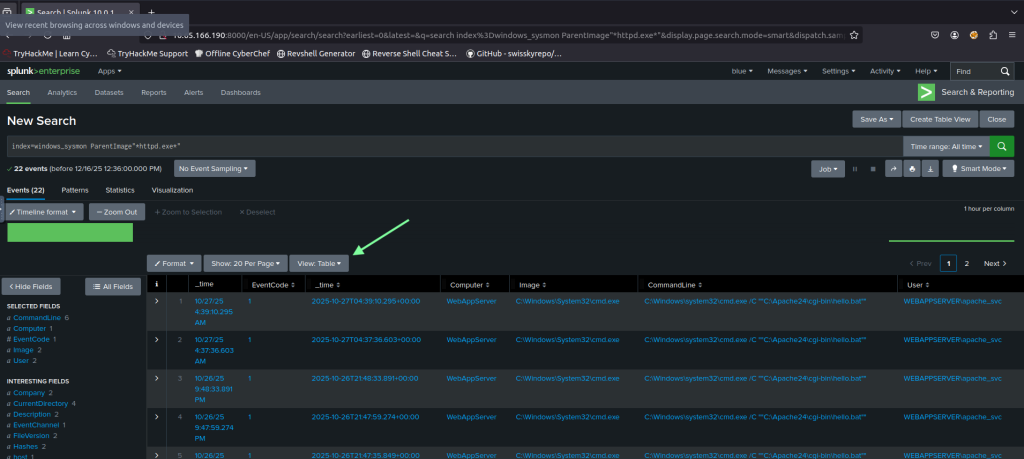
Next, we will look at Sysmon logs. Per THM, “Sysmon refers to System Monitor, which is a Windows system service and device driver developed by Microsoft that is designed to monitor and log various events happening within a Windows system.” Change the View: tab to View: Table.
We make sure our final query returns with “No results found” to confirm are defenses are correctly configured.

This was a simple room that shows the power of Splunk and query’s. I recommend watching the THM walkthrough from CYBERWOX: https://www.youtube.com/watch?v=Gf68YnVjy7k. He breaks down the query’s and elaborates on a lot of things the room does not cover.