https://tryhackme.com/room/xss-aoc2025-c5j8b1m4t6
Room created by: tryhackme, melmols, elgorft2360
“After last year’s automation and tech modernization, Santa’s workshop got a new makeover. McSkidy has a secure message portal where you can contact her directly with any questions or concerns. However, lately, the logs have been lighting up with unusual activity, ranging from odd messages to suspicious search terms. Even Santa’s letters appear to be scripts or random code. Your mission, should you choose to accept it: dig through the logs, uncover the mischief, and figure out who’s trying to mess with McSkidy.”
Navigate to the target machine’s IP address in your Firefox browser.
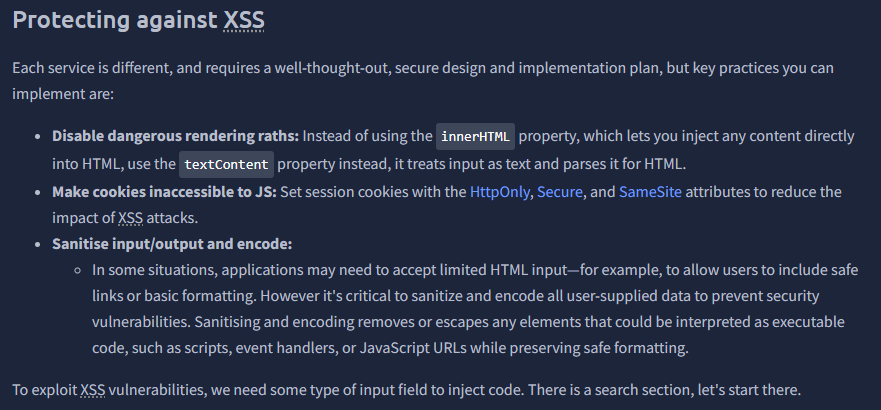
“XSS is a web application vulnerability that lets attackers (or evil bunnies) inject malicious code (usually JavaScript) into input fields that reflect content viewed by other users (e.g., a form or a comment in a blog). When an application doesn’t properly validate or escape user input, that input can be interpreted as code rather than harmless text. This results in malicious code that can steal credentials, deface pages, or impersonate users. Depending on the result, there are various types of XSS. In today’s task, we focus on Reflected XSS and Stored XSS.”
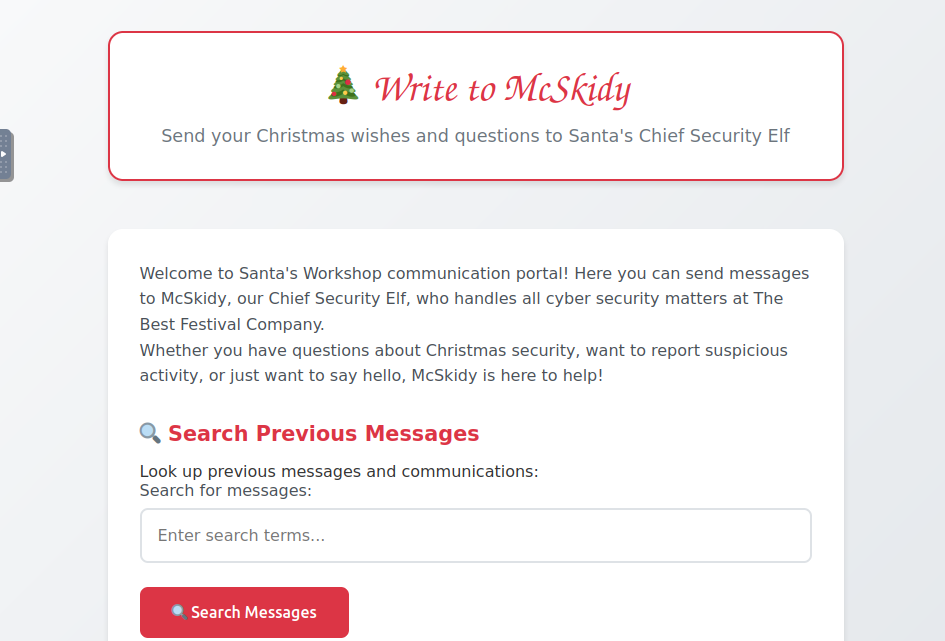
THM has it perform the task of doing a reflected XXS per the search on the website.

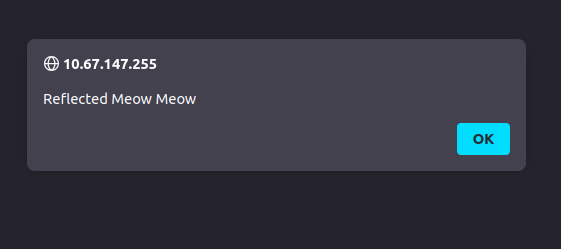
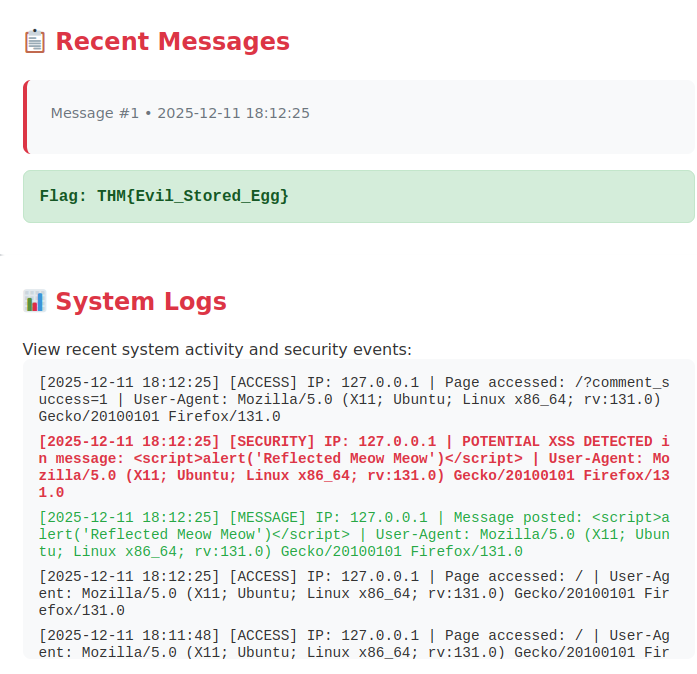
Doing so, we get the flag for the question, “What’s the reflected flag?”

If we look at the System Logs at the bottom of the page, we can see our activity.

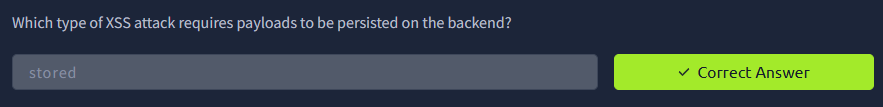
Next up, THM tasks up with performing a Stored XSS attack! Which, btw, is the answer to “Which type of XSS attack requires payloads to be persisted on the backend?”. So any time you hear stored XSS think of persistence.
Instead of the “Search Previous Messages” we are now focusing on the “Send a Message to McSkidy” box.
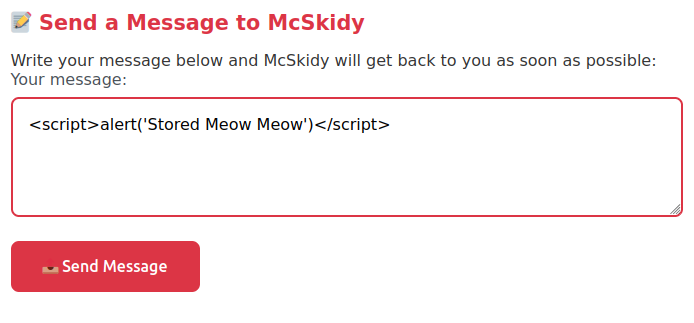
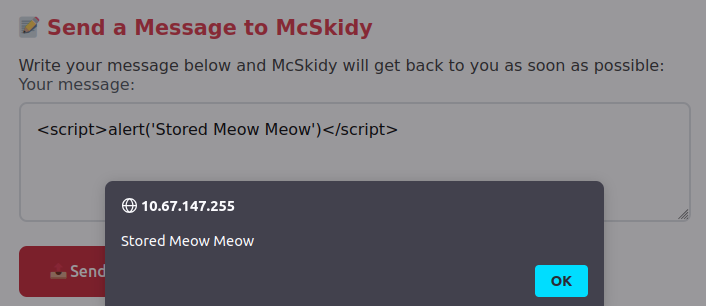
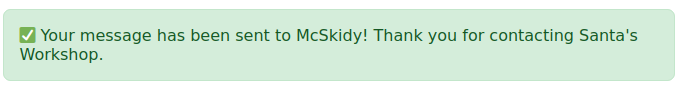
My flag would never populate after I performed the stored attack. I had to disconnect and start up a target instance. After this, the flag was populated along with the System Log event.
THM links to another room that goes deeper into XSS! https://tryhackme.com/room/xss
Snippet highlight: