https://tryhackme.com/room/networkservices-aoc2025-jnsoqbxgky
Created by: Tryhackme, DrGonz0, TactfulTurtle
“Christmas preparations are delayed – HopSec has breached our QA environment and locked us out! Without it, the TBFC projects can’t be tested, and our entire SOC-mas pipeline is frozen. To make things worse, the server is slowly transforming into a twisted EAST-mas node.
Can you uncover HopSec’s trail, find a way back into tbfc-devqa01, and restore the server before the bunny’s takeover is complete? For this task, you’ll need to check every place to hide, every opened port that bunnies left unprotected. Good luck!”

Go ahead and start your target machine, wait for it to load, then go ahead and launch your attacker VM. While that loads, continue on to task 2. THM links to another room that expands on Networking concepts if you are new or need a refresher: https://tryhackme.com/room/networkingconcepts. We are given instructions to note 3 keys as we go along this room.

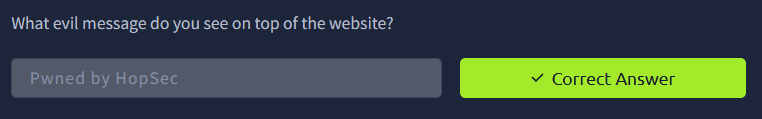
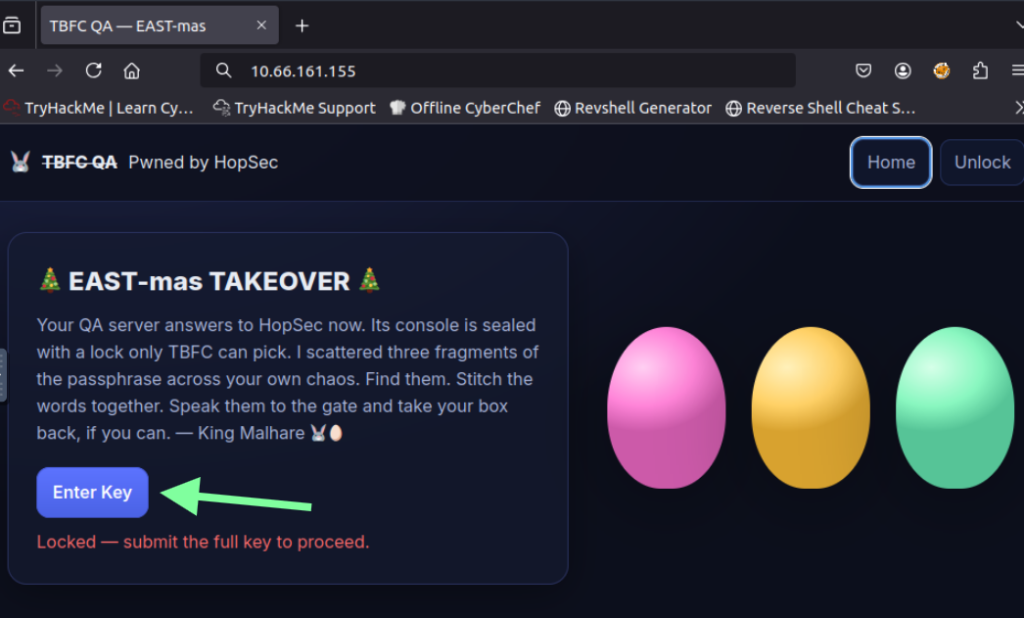
We are going to use the beloved nmap in this room! Running nmap, we see ssh and http ports are open. Because of this, we can visit the target’s IP in the browser to access the website. Doing this, we noticed it’s defaced by the bunnies!


“Pwned by HopSec”!? How rude. This is also the first answer to our question.
Now we are going to get more technical with nmap.

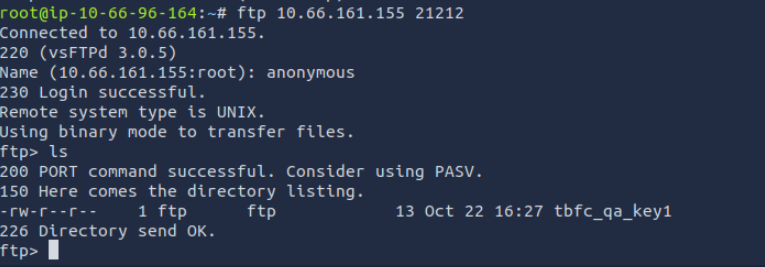
Running this command will take a while, so grab yourself some hot chocolate and sit and wait. We see that they have changed the port number of FTP from 21 to 21212.

THM now wants us to access FTP with the name: anonymous with our newfound knowledge. Doing this, we see key number 1!
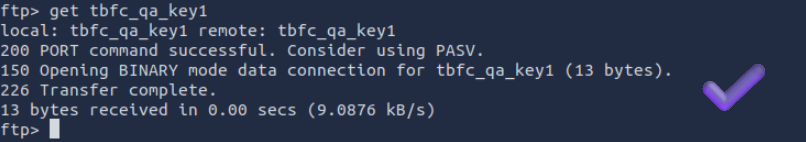
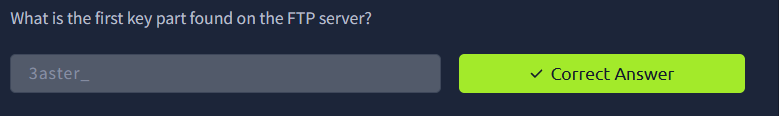
Exit out of the ftp connection with the “!” character. After this, let’s look at where our key is and open its contents. This will be the answer for “What is the first key part found on the FTP server?”

THM wants us to look at port 25251. Let’s run nmap -p- –script=banner IP ADDRESS again.
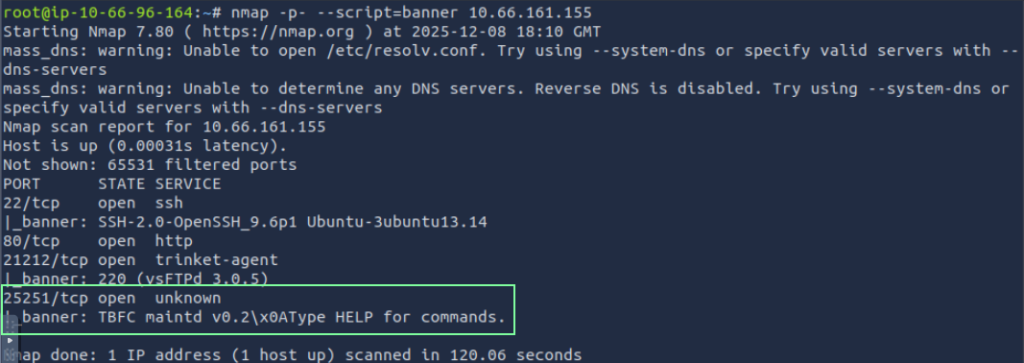
This is a custom port for The Best Festival Company App. Now we are moving from nmap to netcat(nc) to access this.
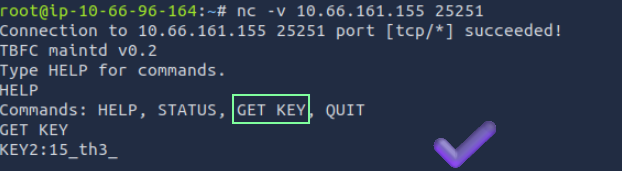
Now we got our second key “What is the third key part found in the DNS records?”

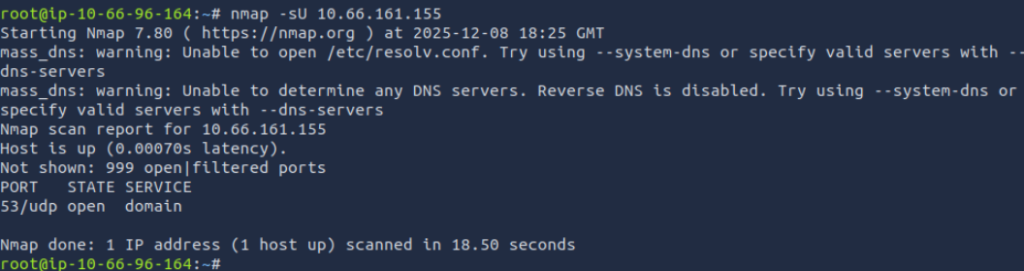
CTRL+C to exit out of Netcat. Back to nmap for the third part of the key. Instead of TCP ports, we are now going to scan for UDP ports. THM then has us use the dig command. We get our answer for “What is the third key part found in the DNS records?”

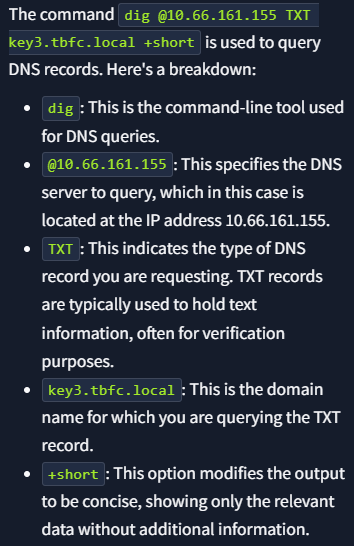
Since THM does not really expand on this command, I had Echo AI break it down for me(something I always recommend if things aren’t too clear for you).

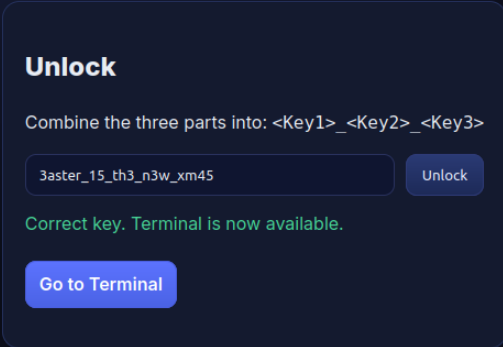
Now that we have our 3 key parts, we can combine them to get: “3aster_15_th3_n3w_xm45” and we need to enter this key to get access to the admin console.
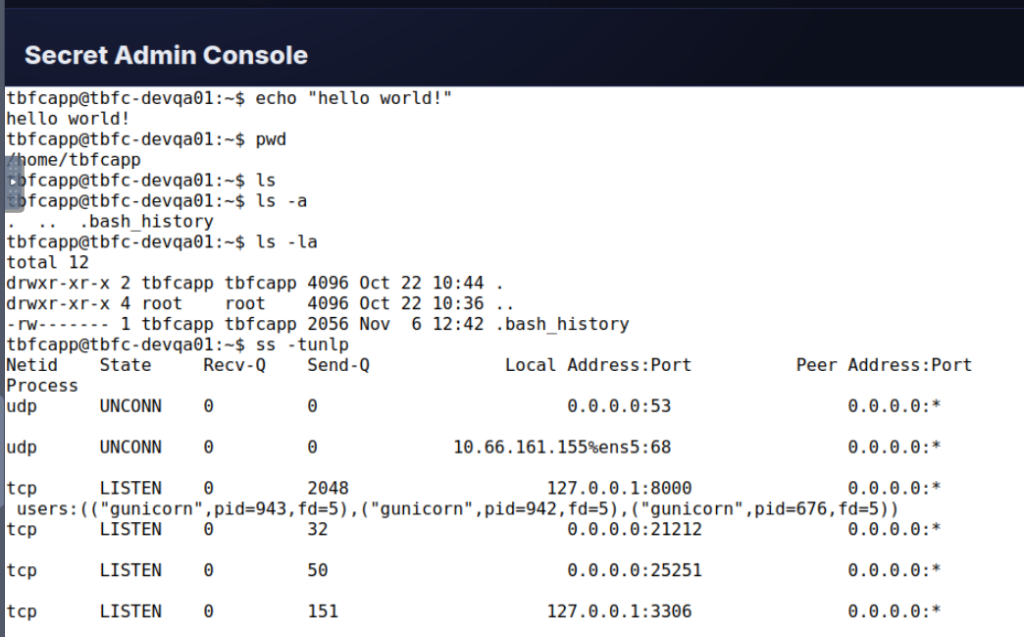
Were focusing on the 127.0.01:3306. 3306 is the default for MYSQL. That will be the answer for “Which port was the MSQL database running on?”.

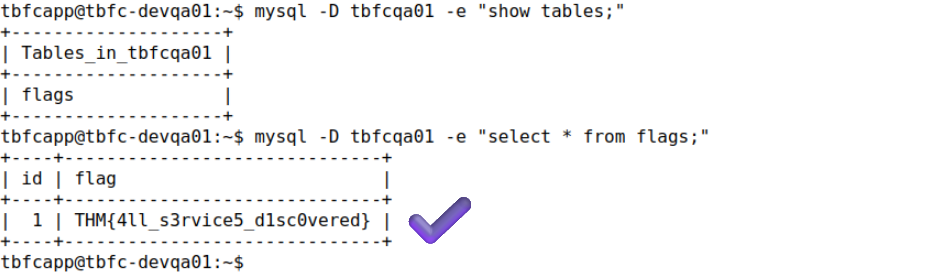
THM wants us to run a mysql command.
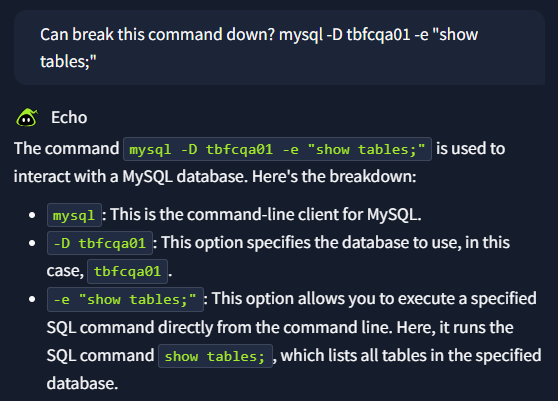
“Finally, what’s the flag you found in the database?”
THM links to Nmap: The Basics https://tryhackme.com/room/nmap. All the nmap rooms on THM are great!