Room link: https://tryhackme.com/room/introtodetectionengineering
Created by: tryhackme, SecurityNomad
While this is not part of the SOC Level 1 path, it was recommended at the beginning of the room “Introduction to SOAR”: https://tryhackme.com/room/soar. I skimmed over the Tasks before I decided that it would be good to complete the room fully, as it seems like a good one.
“Detection engineering is an important role and task for a security analyst. It involves developing processes that will guide you as an analyst to identify threats, detect them through rules and processes, and fine-tune the process as the landscape changes.”
In task 2, “What is Detection Engineering?”, THM brings up two categories when it comes to threat detection: Environment-based detection, “focuses on looking at changes in an environment based on configurations and baseline activities that have been defined. Within this detection, we have Configuration detection and Modelling.” and Threat-based detection, “focuses on elements associated with an adversary’s activity, such as tactics, tools and artefacts that would identify their actions. Under this, we have Indicators and Threat Behavior detections.”
The room covers a good amount of detail when it comes to these as well as Configuration Detection, Modelling, Indicator Detection, Threat Behavior Detection, and Detection as Code.
In Task 3, Detection Engineering Methodologies, THM covers the importance of Gap Analysis and reactive/proactive approaches. The room goes into baseline creations, log collection, rule writing, deployment, automation, and tuning. When it comes to rule writing, THM links to three other rooms we could look at later: https://tryhackme.com/room/snort, https://tryhackme.com/room/yara, and https://tryhackme.com/room/sigma.
In Task 4, a refresher is in store. It covers a little about the MITRE ATT&CK and CAR frameworks, Pyramid of Pain, and Cyber Kill Chain.
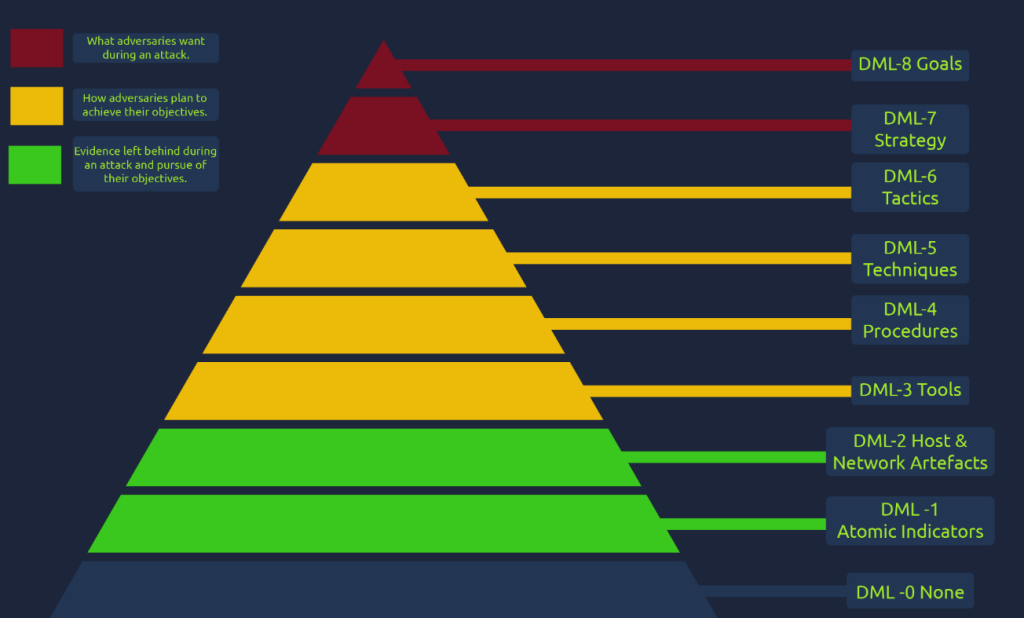
Task 5, “Detection Engineering Frameworks 2,” is more detailed than previous tasks and links to github page: https://github.com/palantir/alerting-detection-strategy-framework by Palantir. The room also goes over Ryan Stillions’ “Detection Maturity Level (DML)” which came out in 2014.

In the final task, “Detection Detective”, we are given a scenario of “THM is seeking to establish a detection engineering process to detect changes made to privileged and administrative groups and accounts in their Active Directory. As a detection analyst, you have been tasked with developing a strategy based on a set of questions. Each question comes with one correct answer; therefore, it is up to you to identify and select it. You will have three attempts to complete the exercise before it resets.”
