https://tryhackme.com/room/auditingandmonitoringse
Created by: tryhackme, strategos

This is a great room and a good refresher for the high-level side of cybersecurity. I also got to do some low-level hands-on log combing with Linux and Windows. Task 1 briefly covers auditing and monitoring. Later, it goes into more details. With that, I obtain the answer to the first two questions.
“What do you call the systematic review of an organisation’s technological infrastructure, policies and operations?”
Auditing is a systematic, independent, and objective process of gathering and evaluating evidence to determine if an organisation, its policies, processes, controls, or financial statements comply with applicable laws, regulations, and industry standards.
“What do you call the continuous observation of an organisation’s computer technologies and related resources?”
Monitoring is about continually checking a computer’s or network’s performance and behaviour. It involves watching over various components such as applications, storage, and networking to make sure they’re working well together. Monitoring also looks for unusual behaviour and checks if anything violates established rules or policies.
Task 2 does a great job of covering Audit objectives and Types.


They also cover internal, external, and third-party audits. Per THM, ” Third-party audits: This type of audit is conducted when an organisation needs to assess its IT systems or controls within third parties, such as vendors, service providers, or subcontractors. Third-party audits ensure that the external entities a company relies on adhere to the required security, data protection, and compliance standards, thereby minimizing potential risks and exposures that may arise from their operations.”
“Which type of audit is conducted by independent auditors?”
External audits: External audits are conducted by independent auditors not employed by the organization being audited. These auditors are typically from external accounting or auditing firms, and the primary purpose is to provide an impartial and objective review.
“Which type of audit is conducted by an organisation’s own personnel?”
Internal audits: These are performed by an organization’s personnel or staff members assigned to the internal audit function.
Task 3 covers popular audit frameworks.
COSO: The Committee of Sponsoring Organizations of the Treadway Commission (COSO) is a private-sector initiative that develops frameworks for enterprise risk management, internal control, and fraud deterrence. COSO’s Internal Control-Integrated Framework(opens in new tab) is one of the most widely used frameworks for auditing internal controls. It is typically used in various industries, including financial services, healthcare, and government.
COBIT: The Control Objectives for Information and Related Technology(opens in new tab) (COBIT) is a framework for the governance and management of information and technology (IT). It provides a comprehensive set of control objectives that can be used to assess the effectiveness of an organisation’s IT governance and management practices. It is typically used in various industries, including financial services, healthcare, and government.
ISAE 3402: ISAE3402(opens in new tab) is an international standard that provides guidance on the assurance of controls over financial reporting. Auditors use it to assure of the effectiveness of an organisation’s internal controls over financial reporting. It is typically used in various industries, including financial services, healthcare, and government.
ISO 27001: ISO 27001(opens in new tab) is an international standard for information security management. It provides a set of best practices for information security management. It is typically used in various industries, including financial services, healthcare, and government.
ITIL**: ITIL stands for Information Technology Infrastructure Library. It is a framework of best practices for IT Service Management (ITSM). ITIL is used in auditing to establish a systematic approach for assessing an organisation’s management and governance of IT services. By providing standard practices and criteria, ITIL helps organisations identify areas where their ITSM practices can be improved and to provide recommendations for how to make those improvements.
PCI DSS: The Payment Card Industry Data Security Standard(opens in new tab) (PCI DSS) is a set of security requirements for organisations that accept payment cards. It is designed to protect cardholder data from unauthorised access, use, disclosure, alteration, or destruction. It is typically used in industries that accept payment cards, such as retail, hospitality, and healthcare.
SOX: The Sarbanes-Oxley Act of 2002 (SOX) is a federal law that establishes auditing and financial reporting requirements for public companies. It is designed to protect investors by improving the accuracy and reliability of financial reporting. It is typically used in public companies.
“What is the standard used by organisations that process card payments?”
PCI DSS
“Who developed ITIL?”
TIL was developed by the Central Computer and Telecommunications Agency (CCTA), a government agency in Great Britain, in the late 1980s.
“Who developed COBIT?”
COBIT was developed by ISACA (Information Systems Audit and Control Association) to provide a framework for information technology management and governance
Task 4 covers the audit process and uses COBIT as an example of how it would be applied to an org.

“Which step do we present our findings about non-conformities, weaknesses and issues noted?
4. Reporting
“At which stage does an organisation review the steps based on recommendations for proper and satisfactory implementation?”
5. Follow-up
“At which stage do the auditors establish the audit scope and define its objectives?”
1. Planning
Task 5 covers Logs and also links to another room you can check out. Apparently I’ve already completed it lol. https://tryhackme.com/room/introtologs
Some of the purposes of logging are…
Troubleshooting: Logs can be a valuable tool for troubleshooting errors. For instance, if a server fails to start, we would look at its logs to discover where it failed and what prevented it from starting.
Monitoring: Logs provide plenty of insight into the utilisation of a system’s resources. Consider the case where a server is slow, and we want to discover the bottleneck affecting its performance. The system might run low on memory, or the CPU might reach 100% utilisation for non-trivial durations. Logs can provide the necessary insights to pinpoint and solve the problem.
Auditing: Logs record users’ activities on a given system. On an audited system, we want to know who logged in, what files they accessed, and what changes they made. This information is necessary to audit a system or investigate any incident.
Compliance: Logs can be a requirement to maintain compliance with relevant regulations. For instance, financial institutions need to keep logs of all financial transactions that take place.
In Task 6, I get my hands on log management with Linux.
THM assists with the the cli and using ausearch.

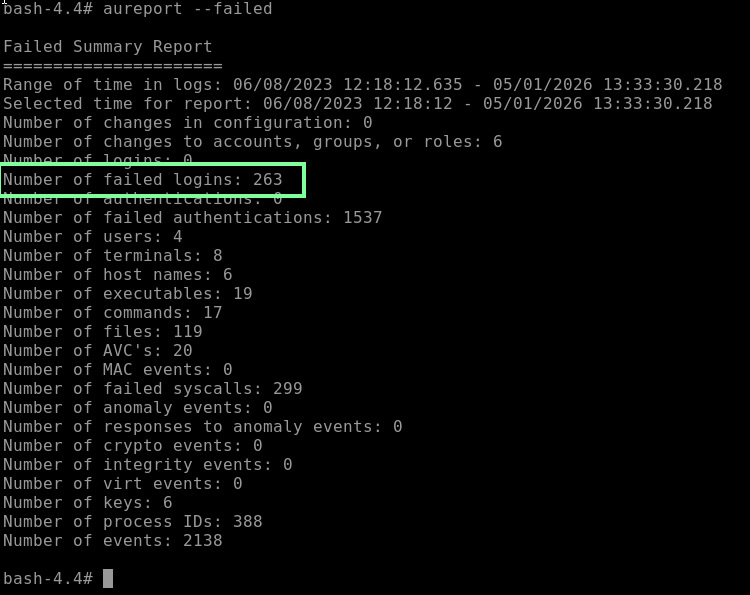
“Using aureport, how many failed logins have occurred so far?”
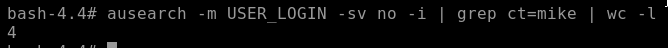
“Using ausearch, how many failed logins are related to the username mike?”
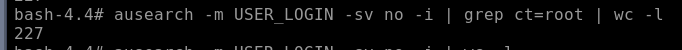
“Using ausearch, how many failed logins are related to the username root?”
Now on to Task 7, Log management on the Windows OS. In order to remote in through the attack box, I use command: xfreerdp /v:IPHERE /u:dawn /p:AuditMe!


“What is the event ID for a failed login attempt?”
4625, as seen above
“How many failed login attempts do you have under the security events?”
Sorting by 4625, we see 2 failed login attempts.
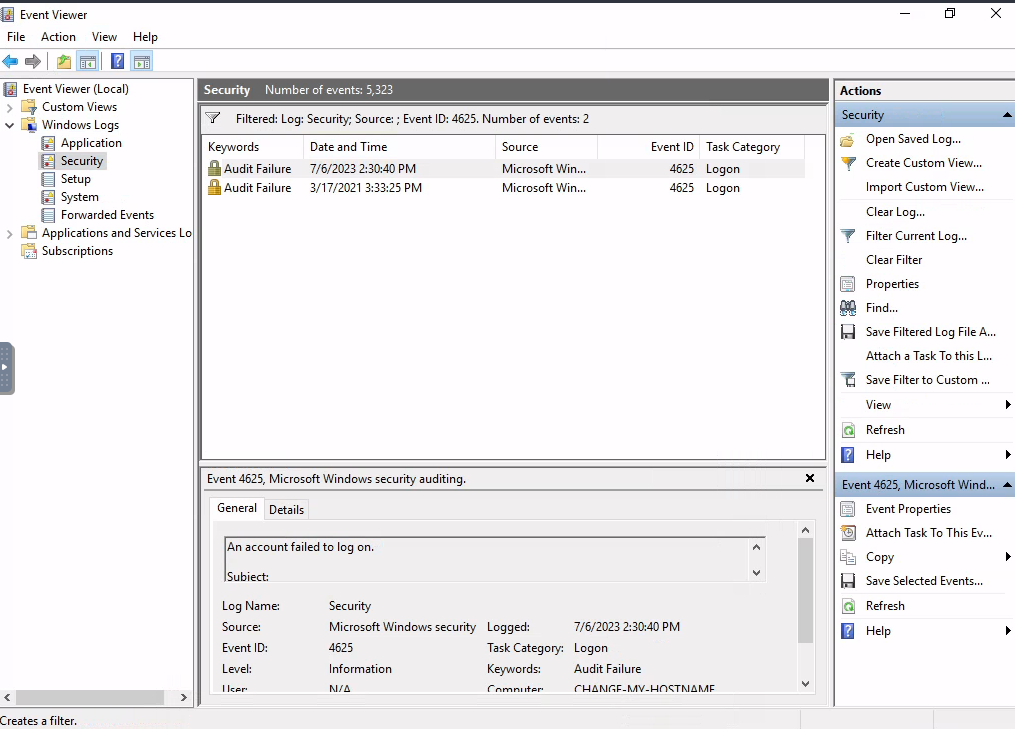
“How many failed login attempts took place in 2021?”
We see above there is only 1. The other failed attempt took place in 2023.
Task 8 covers and presents a nice diagram of differences between logging and monitoring.

SIEM Basics covers the all-mighty SIEM. They also link to two rooms; one that involves Wazuh that I need to tackle soon! https://tryhackme.com/room/wazuhct and https://tryhackme.com/room/splunk101. THM has awesome Splunk rooms!
And another great informative table snippet to the end the room with!
