https://tryhackme.com/room/systemsattackvectors
Room created by: Tryhackme, TactfulTurtle
Introduction: “Continue exploring the SOC role in protecting the digital world, now focusing on systems as attack vectors. In this room, you will learn what the systems are, why and how threat groups target them, and what you can do as a SOC analyst to keep your company secure.”
In the previous room we covered people as attack vectors. In this room we are focusing on systems. Per THM, “…a system: a physical server, a virtual machine, or a cloud platform like Microsoft 365”
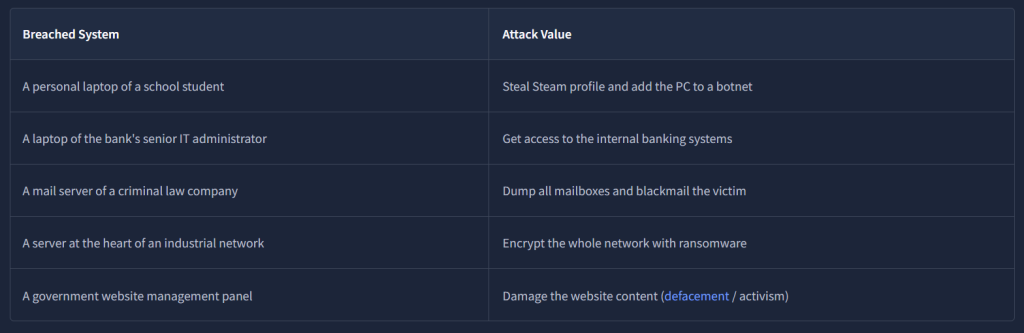
In Task 3, THM gives examples of human-led attacks against systems, as well as vulnerabilities and supply chain attacks. THM even points out they were once victims of a supply chain attack and links to a room that goes into the details of how it happened: https://tryhackme.com/room/supplychainattacks.
In Task 4, regarding software vulnerabilities, they discuss the importance of CVEs. We will need to conduct an investigation to find the answer they are requesting for the ToolShell CVE.

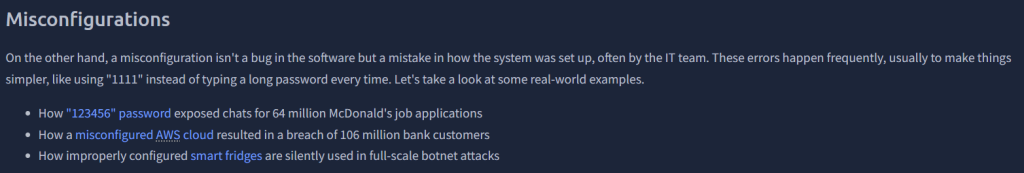
Task 5 is brief and covers Misconfigurations. They go into more detail in the task but the below picture and the examples show just how big an impact misconfigurations can cause.
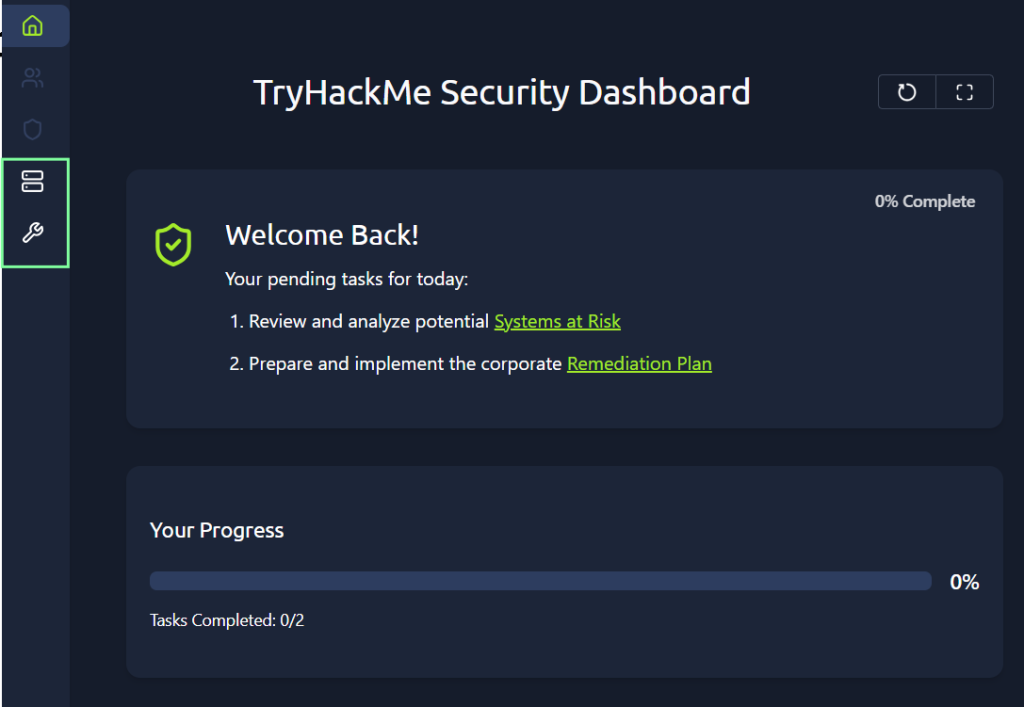
In task 6, Practice, we are presented with a “View Site” lab and explore Systems at Risk as well as Remediation Plans. Again, like in the previous room, “Humans as Attack Vectors”, the remediations are what are needed to put in place to protect the systems at risk.
Again, another brief room, but it gets the point across. After this room, it appears that we are moving on to SOC-level rooms, which will be more technical and present some challenges. The room ends with a few links, I would bookmark them if I were you for future use cases: https://thedfirreport.com/, https://www.cisa.gov/known-exploited-vulnerabilities-catalog, https://www.bleepingcomputer.com/tag/supply-chain-attack/, and https://threatmap.checkpoint.com/.