https://tryhackme.com/room/splunk201
Created by: Tryhackme, Dex01

If you haven’t already, finish this room first before continuing with this one: https://tryhackme.com/jr/splunk101. Before we get into Splunk, THM quickly goes over the Incident handling life cycle as well as the cyber kill chain.


Now it’s time to go and investigate the attacker’s Reconnaissance Phase with Splunk!
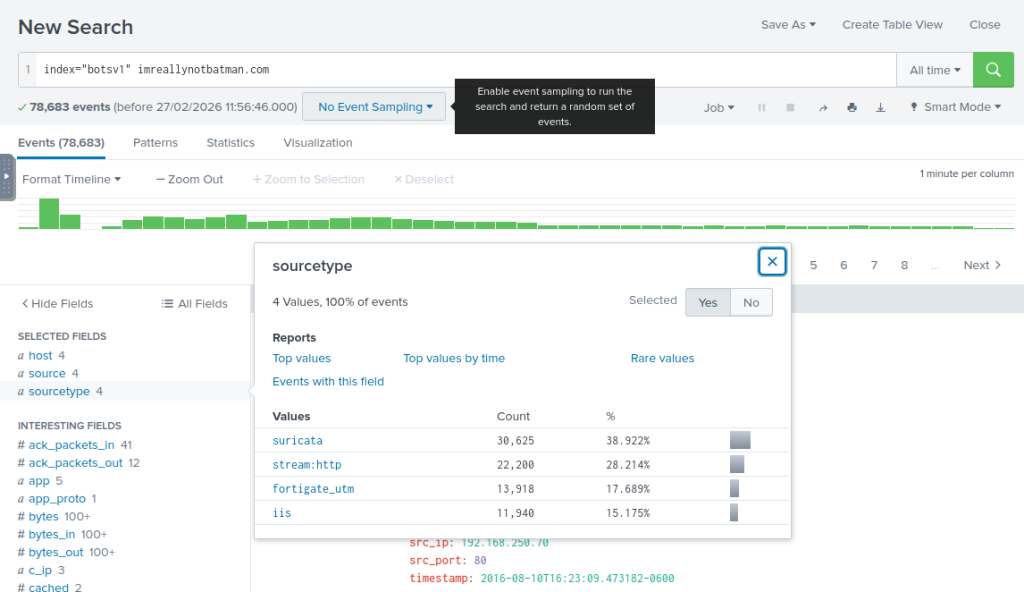
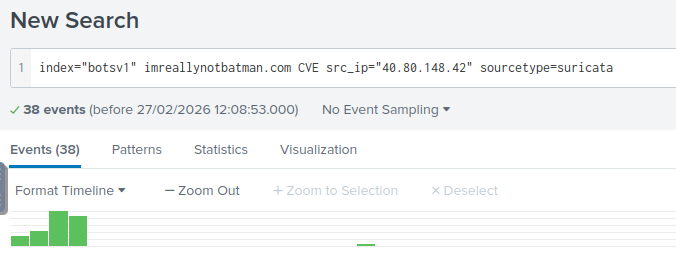
“One suricata alert highlighted the CVE value associated with the attack attempt. What is the CVE value?”

“What is the CMS our web server is using?”
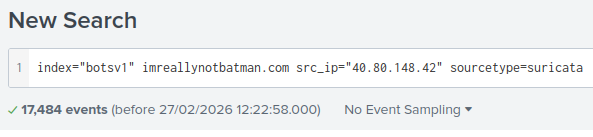
“What is the web scanner, the attacker used to perform the scanning attempts?”
Click on “Show as raw text” with this search filter.

“What is the IP address of the server imreallynotbatman.com?”

Now to investigate the exploit’s the attacker had made. We start to get down in the weeds of Splunk in this task. THM covers a lot. I recommend going along with the search filters and playing around with them.
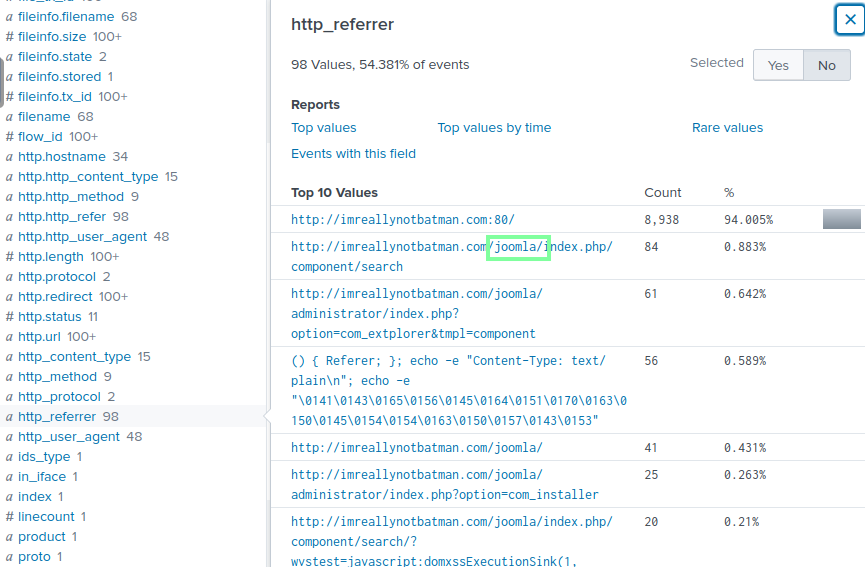
“What was the URI which got multiple brute force attempts?”

“Against which username was the brute force attempt made?”

“What was the correct password for admin access to the content management system running imreallynotbatman.com?”

“How many unique passwords were attempted in the brute force attempt?”
413-1 successful password=412.

“What IP address is likely attempting a brute force password attack against imreallynotbatman.com?”

“After finding the correct password, which IP did the attacker use to log in to the admin panel?”

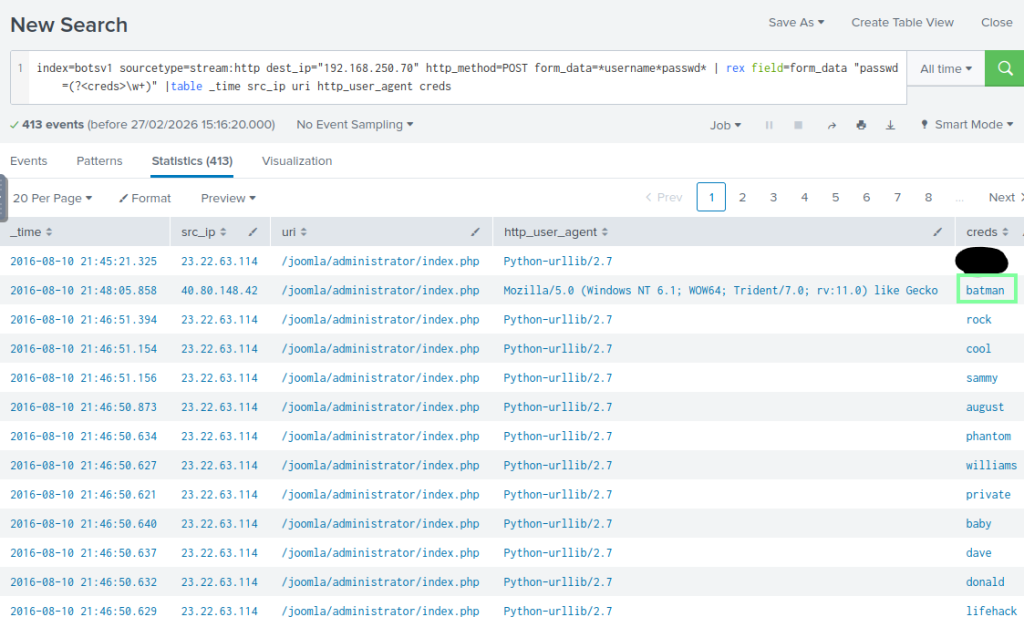
Now, let’s look at the “Installation Phase” that the adversary has performed!

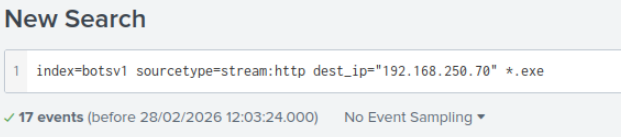


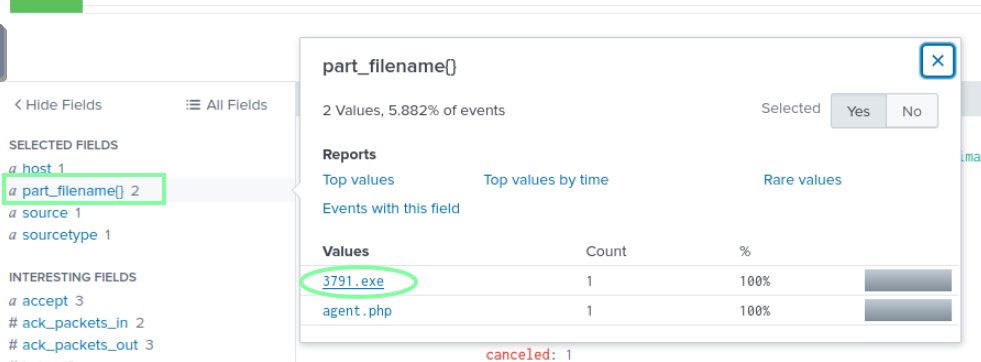
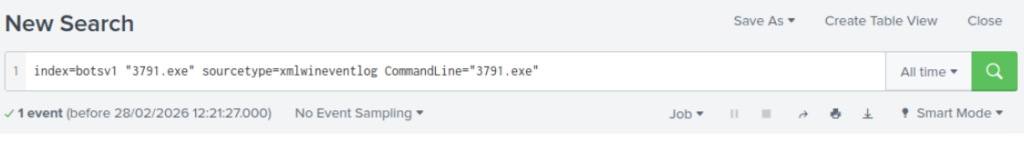
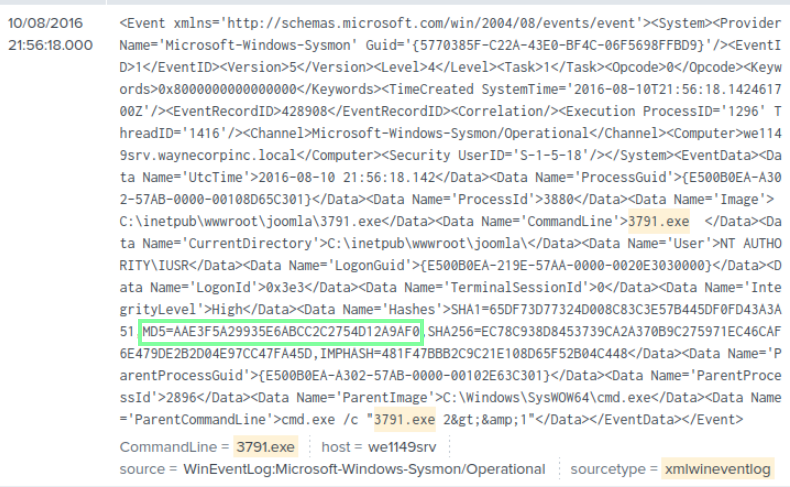
“Sysmon also collects the Hash value of the processes being created. What is the MD5 HASH of the program 3791.exe?”
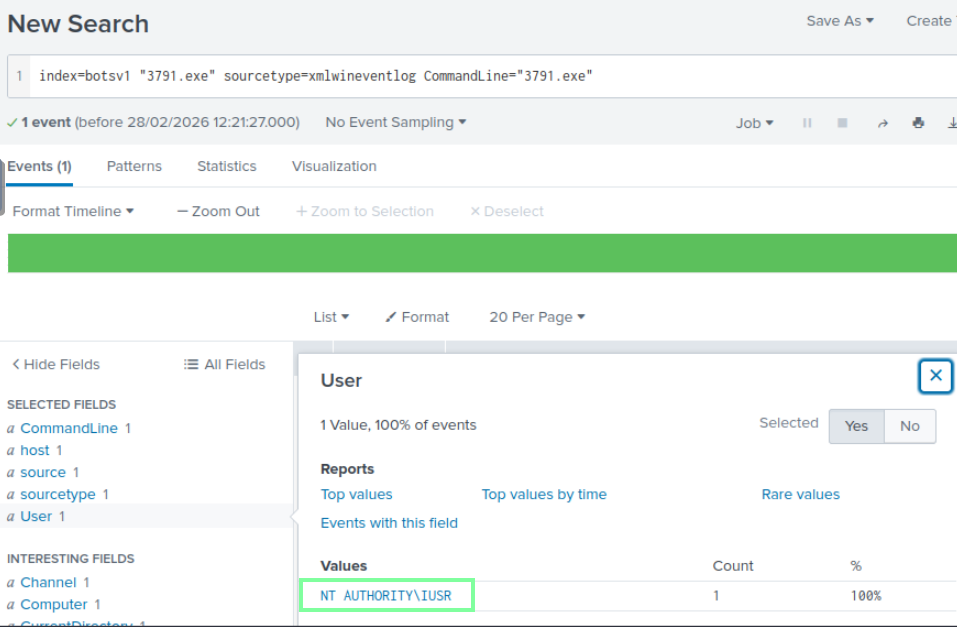
“Looking at the logs, which user executed the program 3791.exe on the server?”
“Search hash on the virustotal. What other name is associated with this file 3791.exe?”

Now on to Task 7, Action on Objectives!

“What is the name of the file that defaced the imreallynotbatman.com website ?”

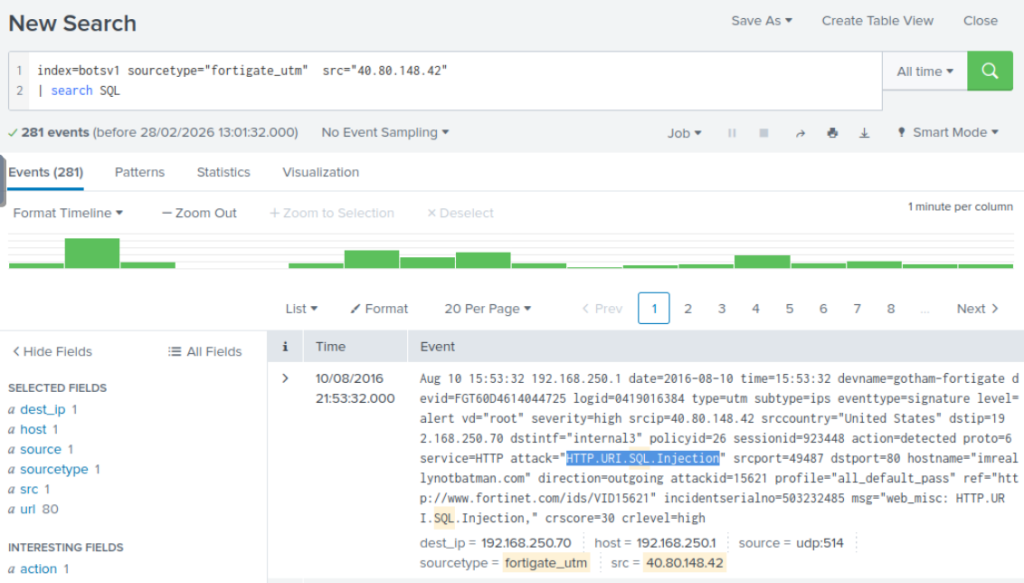
“Fortigate Firewall ‘fortigate_utm’ detected SQL attempt from the attacker’s IP 40.80.148.42. What is the name of the rule that was triggered during the SQL Injection attempt?”
On to Task 8, Command and Control Phase! This is quicker task but we have are closing in on the gap of the attackers steps so it makes sense.

“This attack used dynamic DNS to resolve to the malicious IP. What fully qualified domain name (FQDN) is associated with this attack?”

On to task 9, Weaponization Phase!

For this task, we will be doing OSINT. The 3 sites we will be using are: https://www.robtex.com/, https://www.virustotal.com/, and https://whois.domaintools.com/. FYI the site they want us to visit does not have a whoisrecord anymore with whois.
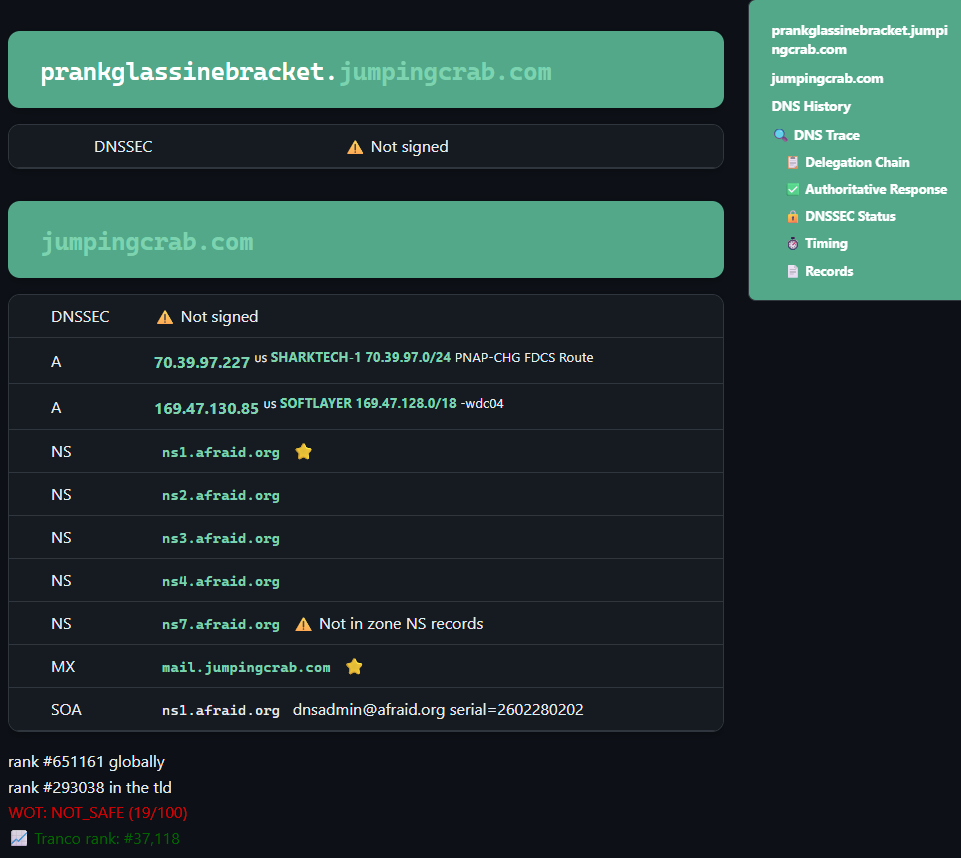
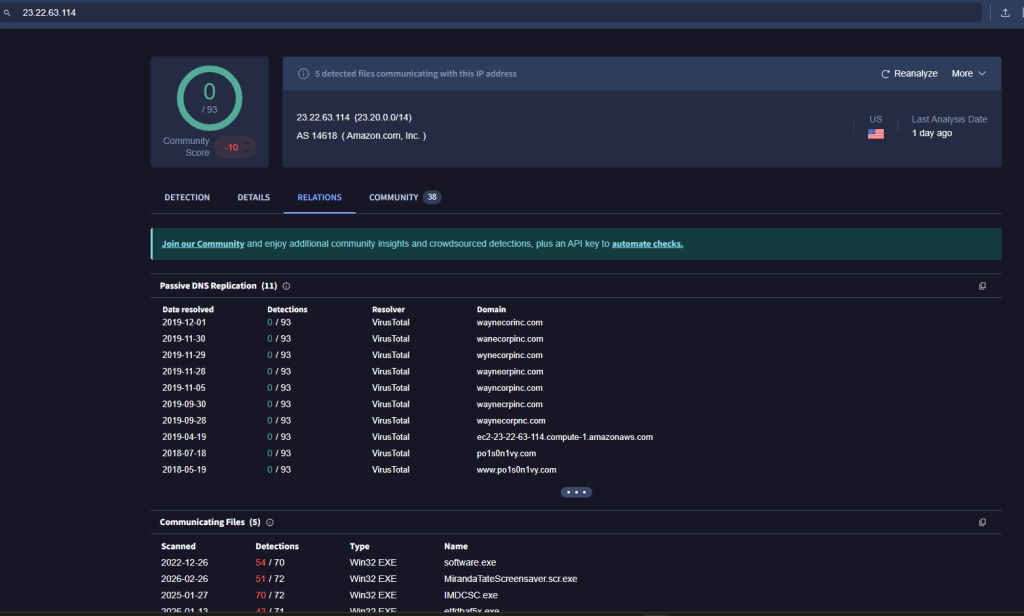
“What IP address has P01s0n1vy tied to domains that are pre-staged to attack Wayne Enterprises?”
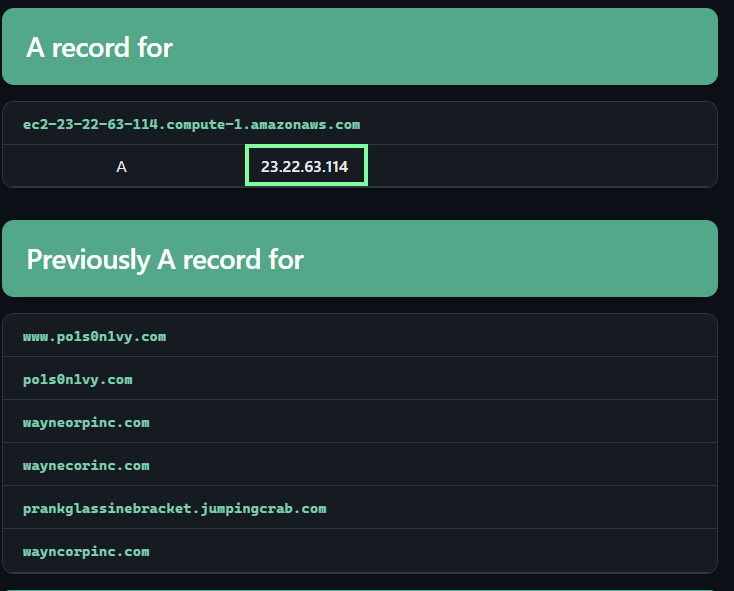
“Based on the data gathered from this attack and common open-source intelligence sources for domain names, what is the email address that is most likely associated with the P01s0n1vy APT group?”
This question needs to be updated as the sites and related resources do not give us the correct answer. I went through various websites and even the suggested one. Had to look up a walkthrough to obtain the answer.

On to our last task, Task 10 Delivery Phase!
https://www.threatminer.org/host.php?q=23.22.63.114#gsc.tab=0&gsc.q=23.22.63.114&gsc.page=1, http://virustotal.com/, and https://www.hybrid-analysis.com/sample/9709473ab351387aab9e816eff3910b9f28a7a70202e250ed46dba8f820f34a8?environmentId=100 will be our resources.
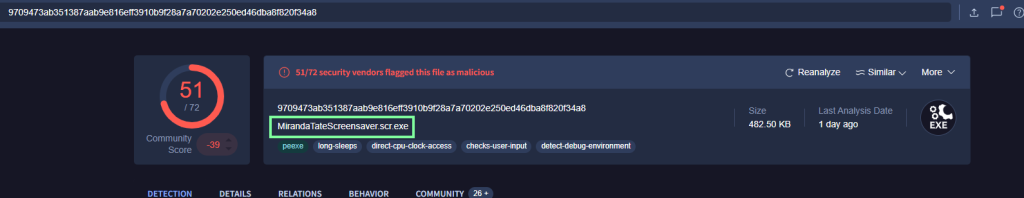
“What is the HASH of the Malware associated with the APT group?”

“What is the name of the Malware associated with the Poison Ivy Infrastructure?”