https://tryhackme.com/room/invite-only
Created by: tryhackme, SecurityNomad, Gensane
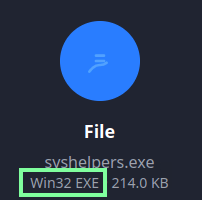
“What is the name of the file identified with the flagged SHA256 hash?”
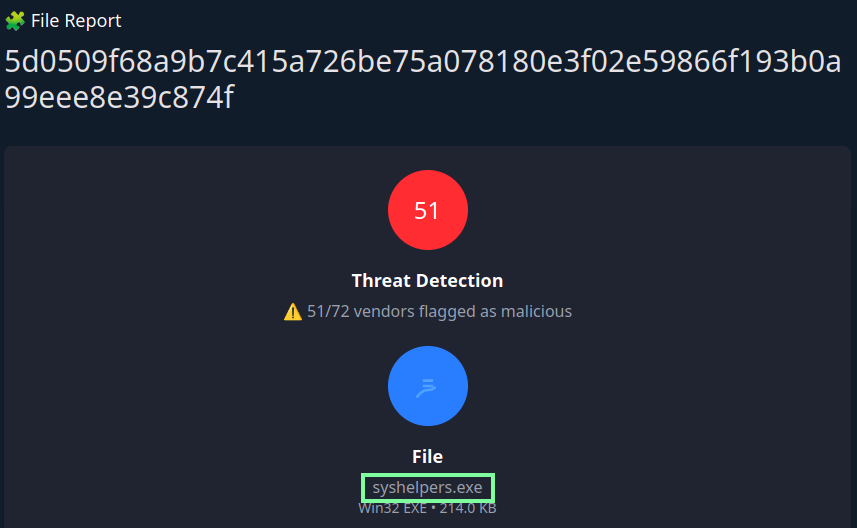
“What is the file type associated with the flagged SHA256 hash?”
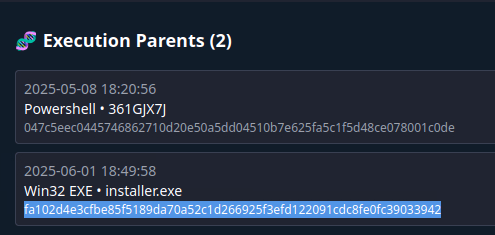
“What are the execution parents of the flagged hash? List the names chronologically, using a comma as a separator. Note down the hashes for later use.”
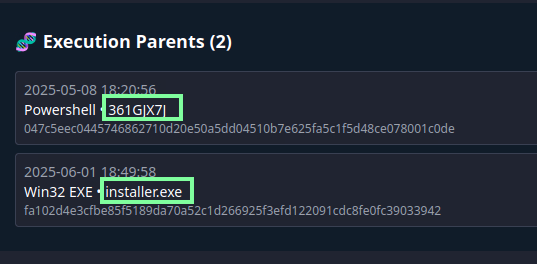
047c5eec0445746862710d20e50a5dd04510b7e625fa5c1f5d48ce078001c0de
fa102d4e3cfbe85f5189da70a52c1d266925f3efd122091cdc8fe0fc39033942
“What is the name of the file being dropped? Note down the hash value for later use.”
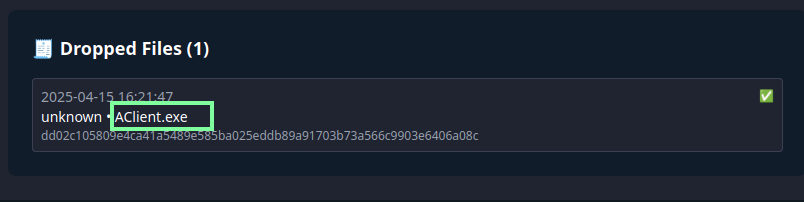
dd02c105809e4ca41a5489e585ba025eddb89a91703b73a566c9903e6406a08c
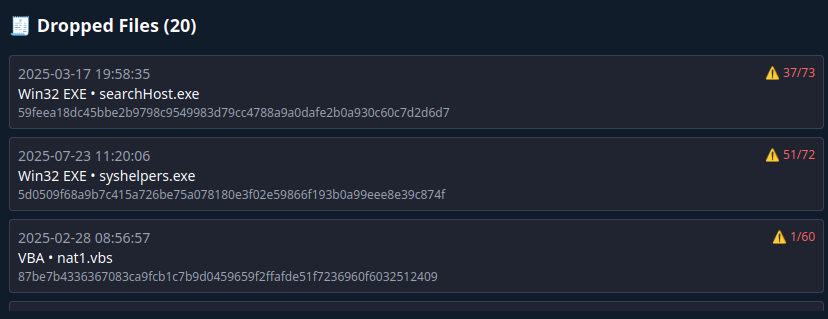
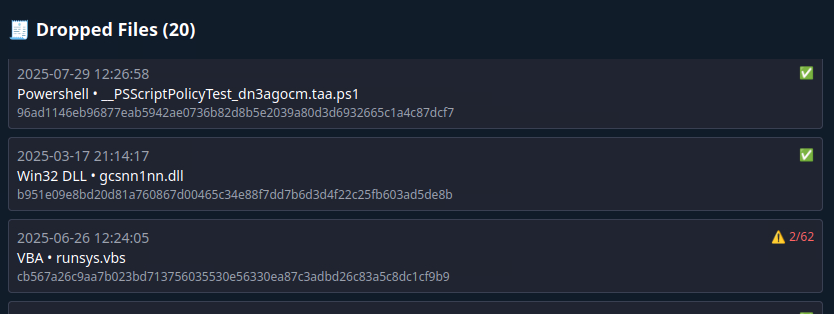
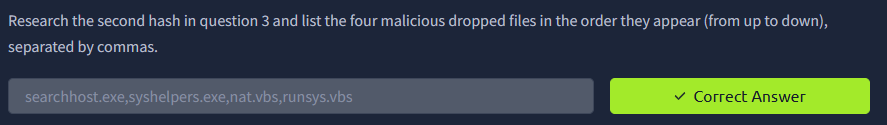
“Research the second hash in question 3 and list the four malicious dropped files in the order they appear (from up to down), separated by commas.”
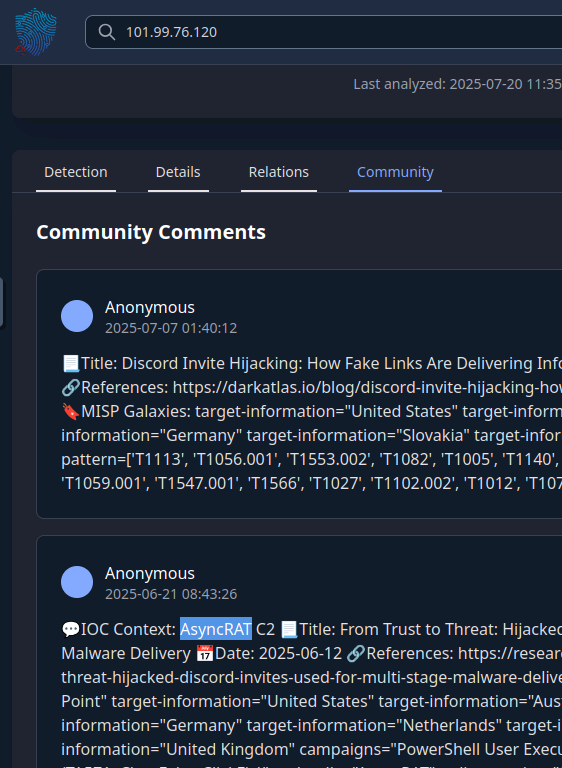
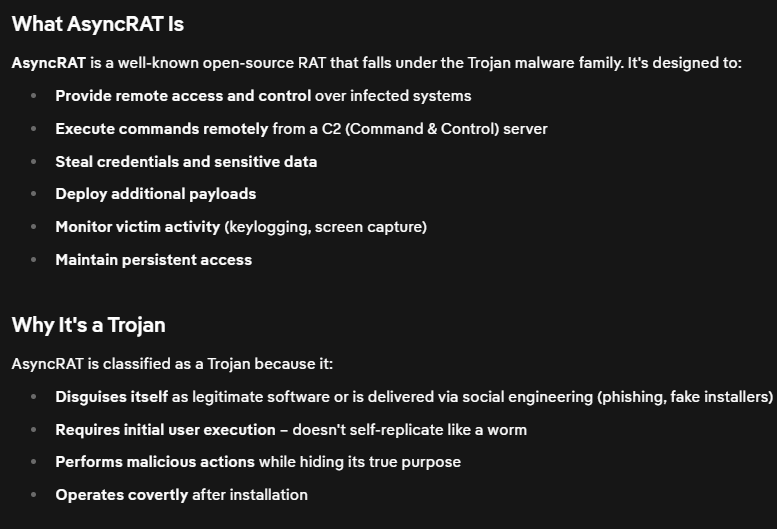
“Analyse the files related to the flagged IP. What is the malware family that links these files?”
At first, I searched the hashes of the files and found the common link that they are Trojans but THM was wanting something more specific. Using the flagged IP address, I was able to find the answer in the Community section.

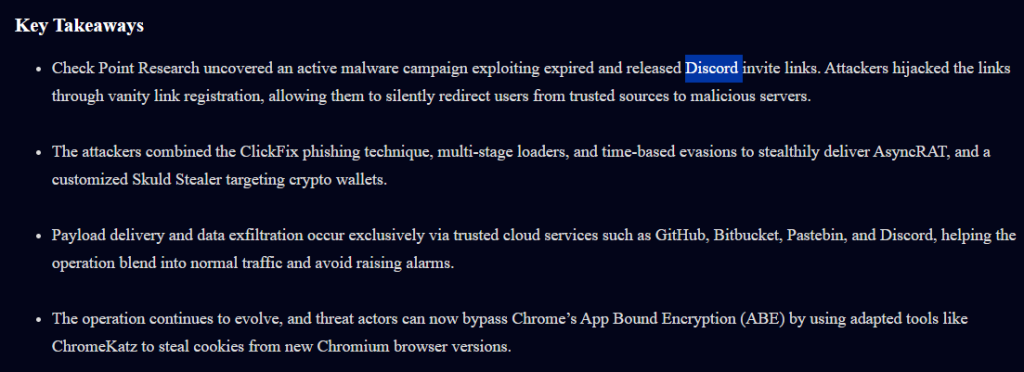
“What is the title of the original report where these flagged indicators are mentioned? Use Google to find the report.”
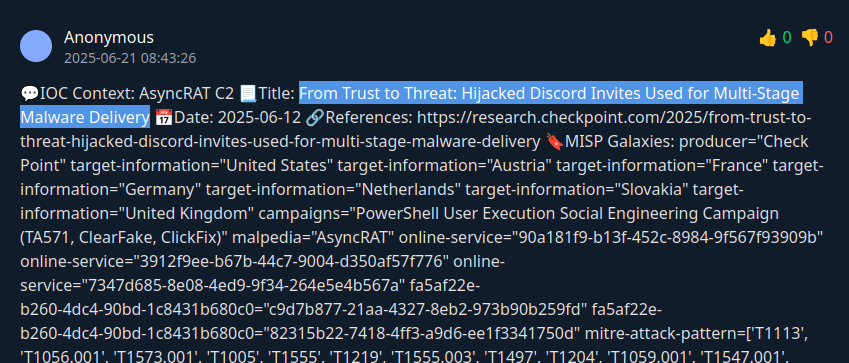
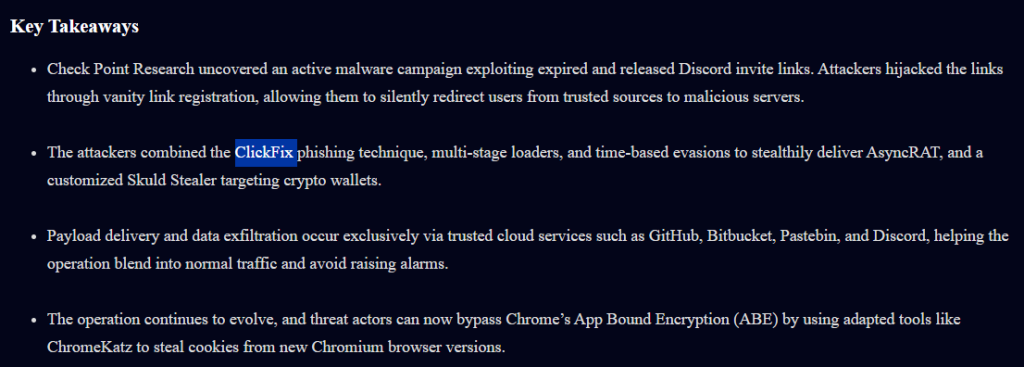
“Which tool did the attackers use to steal cookies from the Google Chrome browser?”
Going to the referenced link to the article:
https://research.checkpoint.com/2025/from-trust-to-threat-hijacked-discord-invites-used-for-multi-stage-malware-delivery
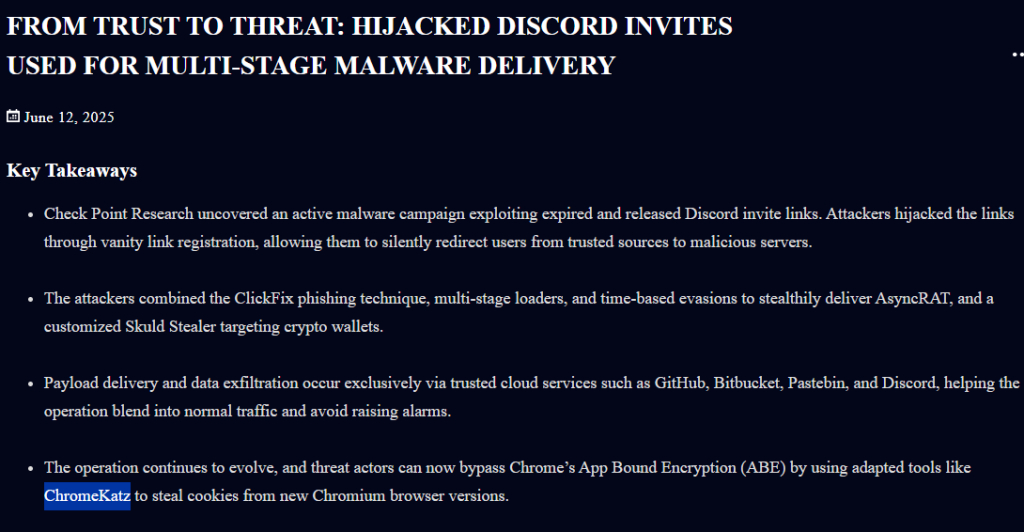
“Which phishing technique did the attackers use? Use the report to answer the question.”
“What is the name of the platform that was used to redirect a user to malicious servers?”