https://tryhackme.com/room/alerttriagewithelastic
Created by: tryhackme, ryla, TactfulTurtle
Note: Apologies about the text being so small/blurry! I tried a different image format size to help with that. Next time, I will enhance the zoom in my browser, which should help with the text size.
“How many logs are available for analysis within the entire time range?”

“What is the field value for the client.ip in the weblogs index?”

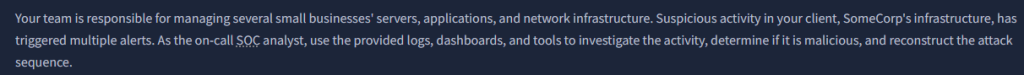
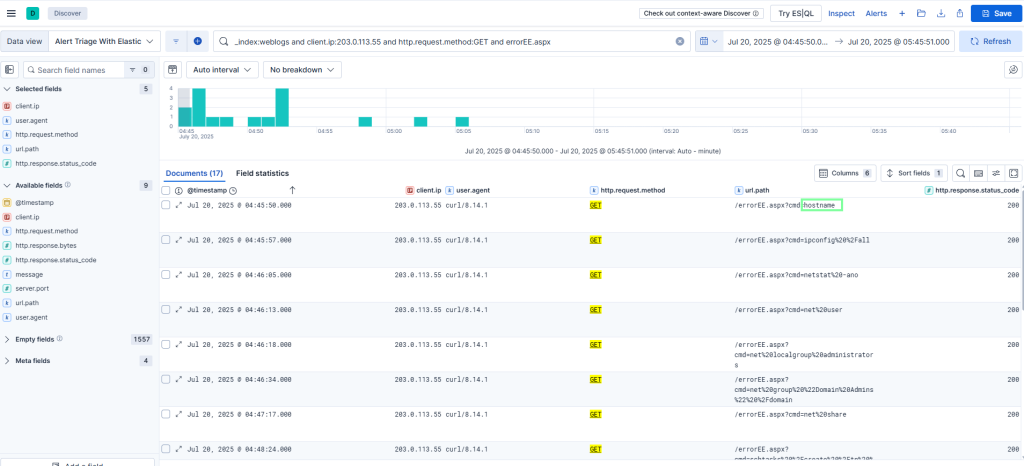
In Task 3, THM has us filter a few searches through ELK.

THM has us update our search filter as well as our “Selected field” section and to sort the list.

“How many POST requests did the IP address 203.0.113.55 make to proxyLogon.ecp?”

“Which user.agent paired with the IP address 203.0.113.55 made the POST requests?”
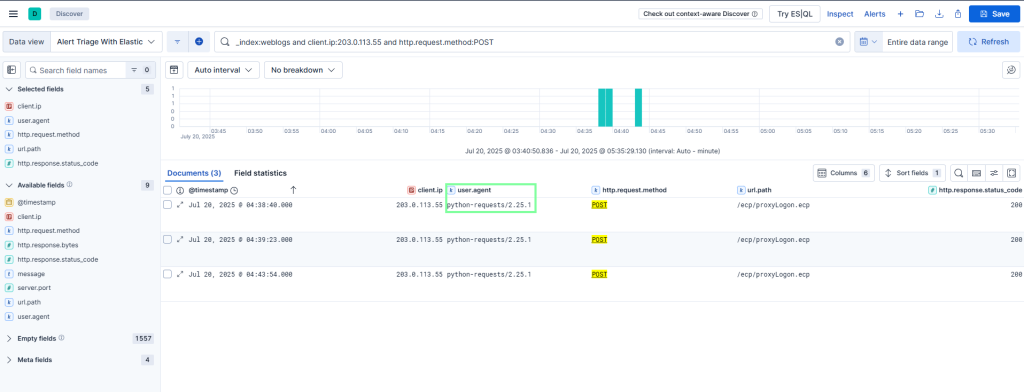
“How many logs contain the cmd= query parameter in the url.path field?”
“Which command was run utilizing errorEE.aspx on Jul 20, 2025 @ 04:45:50.000?”
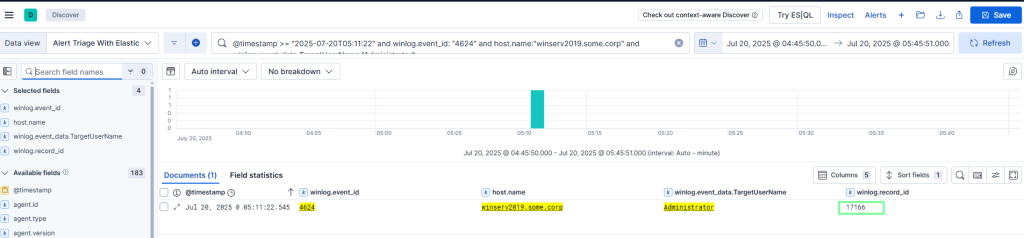
On to task 4 Uncovering Account Activity!
“What is the winlog.record_id of the Administrator 4624 logon event?
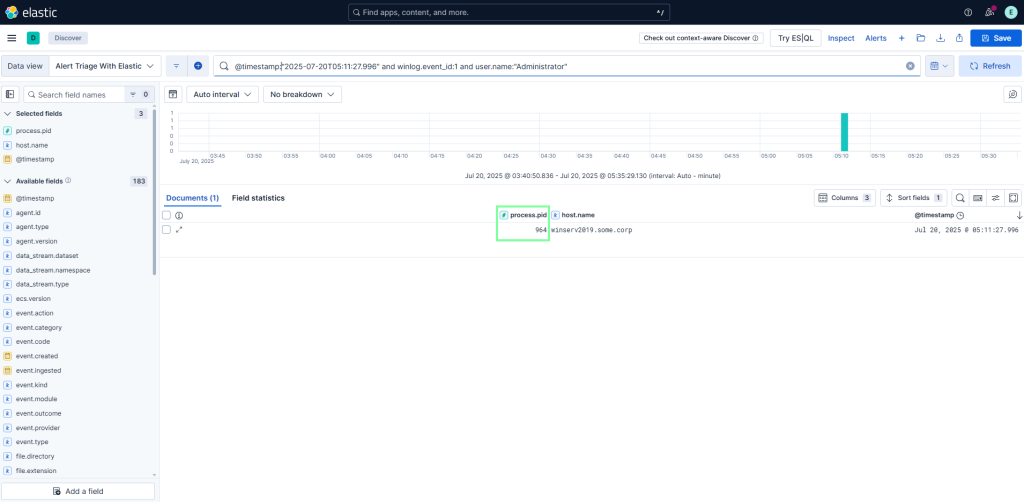
“What is the process.pid of the Sysmon 1 event that occurred on Jul 20, 2025 @ 05:11:27.996?”
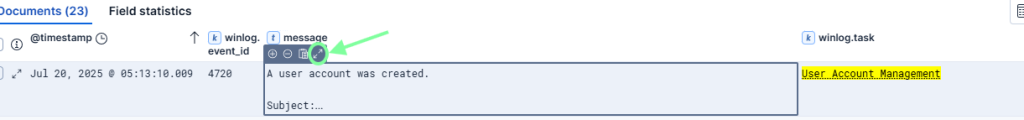
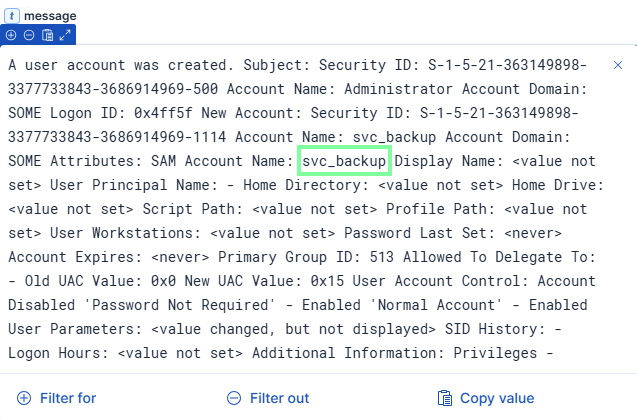
“What is the winlog.event_id for the new user account being created?”

“What is the name of the new user account?”
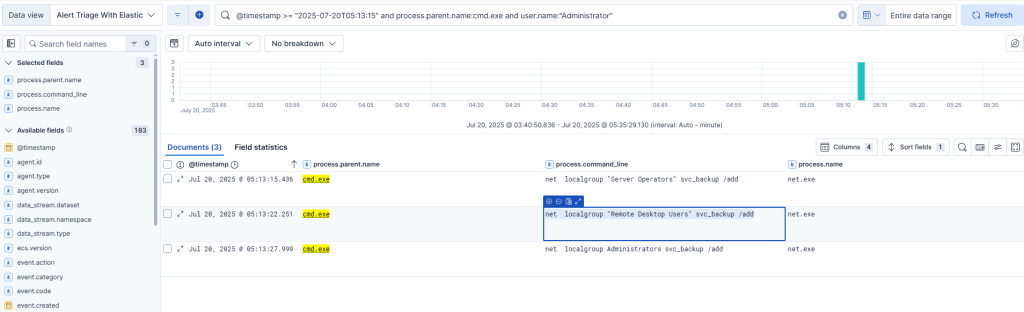
On to the last task of the room, Exposing Command Execution!
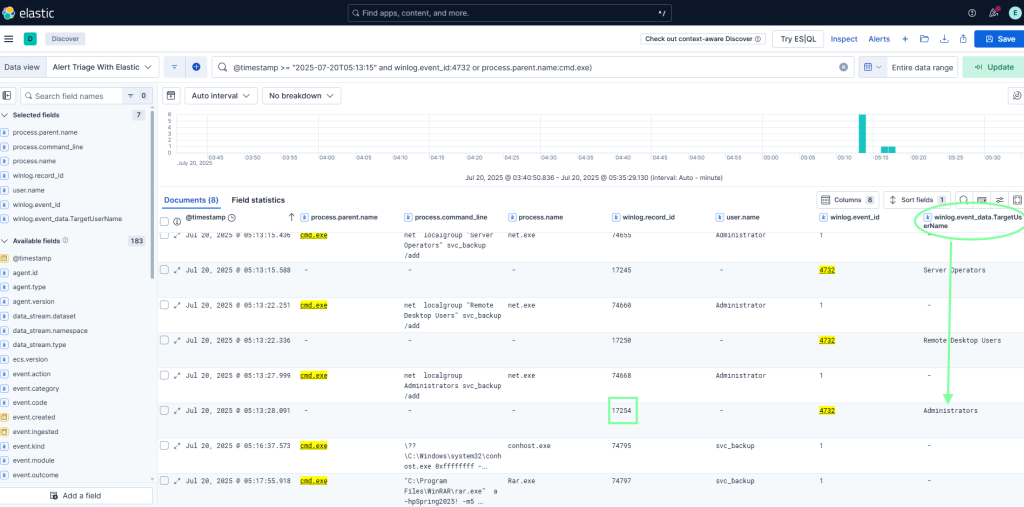
“What command does the attacker use to add the new account to the “Remote Desktop Users” group?”
“What is the winlog.record_id of the 4732 Security event when the attacker adds the user to the Administrator group?”
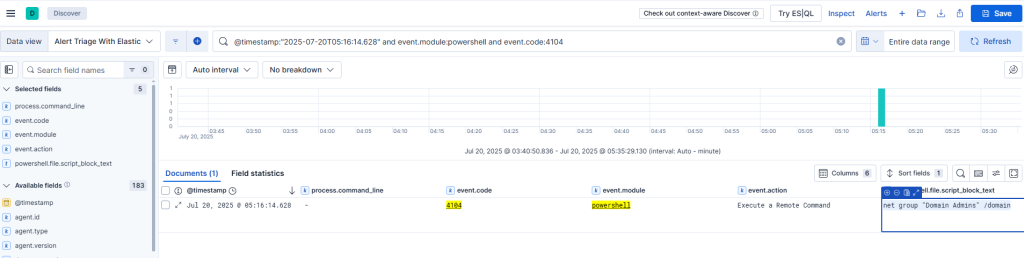
“What PowerShell command did the attacker run on Jul 20, 2025 @ 05:16:14.628?”
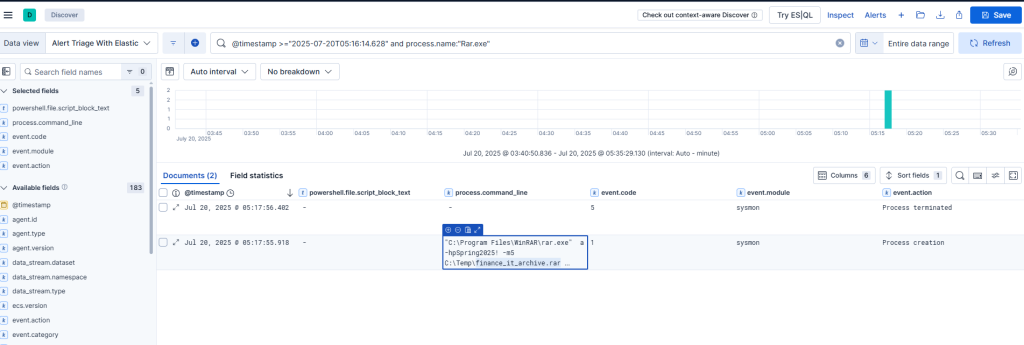
“What is the name of the archive that the attacker creates using the Rar.exe executable?”