https://tryhackme.com/room/cyberthreatintel
Created by: tryhackme, SecurityNomad, TactfulTurtle

There’s a lot of great reading material in this room(which means a lot of snippets!)

On to Task 3, CTI Lifecycle!
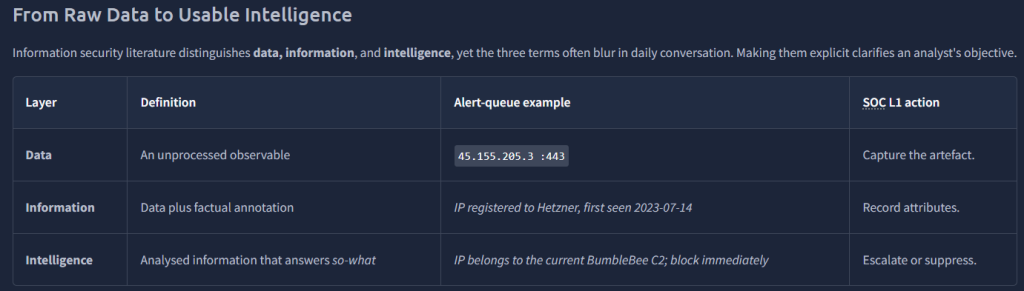
THM presents a fictional scenarior that cover the phases of the CTI lifecycle. Per THM, “Cyber Threat Intelligence follows a six-phase intelligence lifecycle that transforms raw data into contextualized and action-oriented insights geared towards triaging security incidents.”
My simplified version of what THM presents:
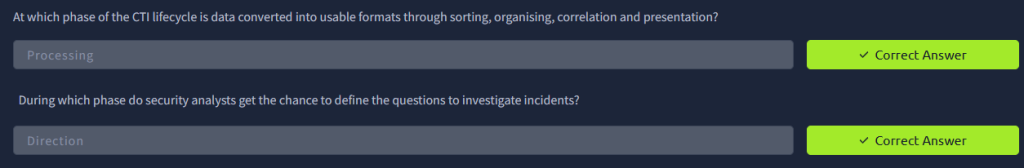
Step 1. Direction – Defining the Mission(Planning)
Step 2. Collection – Assembling the Raw Material(Gathering intelligence from different sources)
Step 3. Processing – Normalizing and Correlating the Data(Ensure data is converted into a standardized readable format)
Step 4. Analysis – Turning Information Into Judgement – (Applying the previous steps to the suspected malicious indicators or artifacts)
Step 5. Dissemination – Getting Intelligence to the Right Consumers(Give the information we now have to the Firewall team, endpoint team, CTI platform, and Management team for them to use within their workflow)
Step 6. Feedback – Measuring and Refining the Cycle (Metric and reports to showcase the effectiveness of the implantation of the steps)
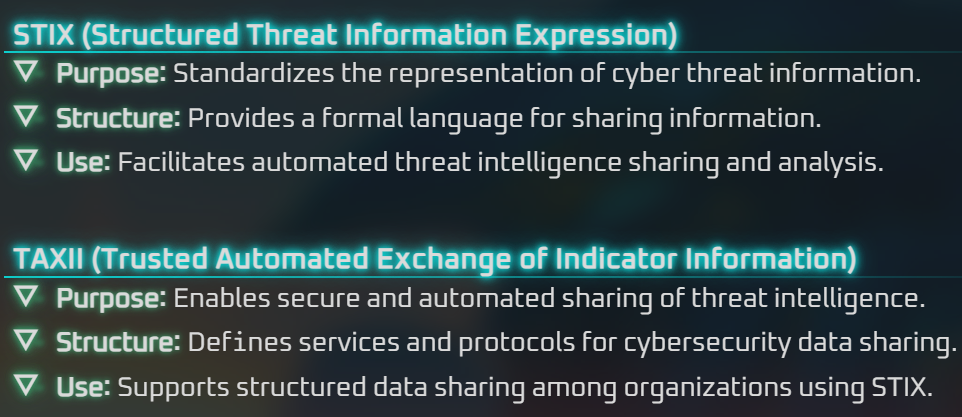
On to Task 4, CTI Standards and Frameworks! This room covers the MITRE ATT&CK framework , MITRE D3FEND, Cyber Kill Chain, CVEs, CVSS, and the NVD, STIX and TAXXII. With the help from Duck.ai here’s a simple bullet form of each:




On to Task 5, Practical Analysis!
“What was the source email address?”

“What was the name of the file downloaded?”

“After building the threat profile, what message do you receive?”
You must answer each of the questions that THM has set up. So far we have the threat actor email and the tool/exe. The IP questions are obvious. The email recipient is John Doe and the account that was compromised was Administrator.
