https://tryhackme.com/room/detectingwebattacks
Created by: tryhackme, ryla, TactfulTurtle

THM links to other rooms per the prerequisites. These rooms cover the most recent update to OWASP!
“OWASP Top 10 covers the ten most critical web security risks. Complete Intro to Log Analysis for an overview of logs and useful indicators. Wireshark: The Basics provides a great introduction to packet capture analysis.”
Task 2: Client-Side Attacks!
Before we address our questions, THM links to two other rooms: https://tryhackme.com/room/axss for XSS attacks and https://tryhackme.com/room/csrfV2 for CSRF attacks.
For questions “What class of attacks relies on exploiting the user’s behavior or device?” and “What is the most common client-side attack?”

On to Task 3, Server-Side Attacks!

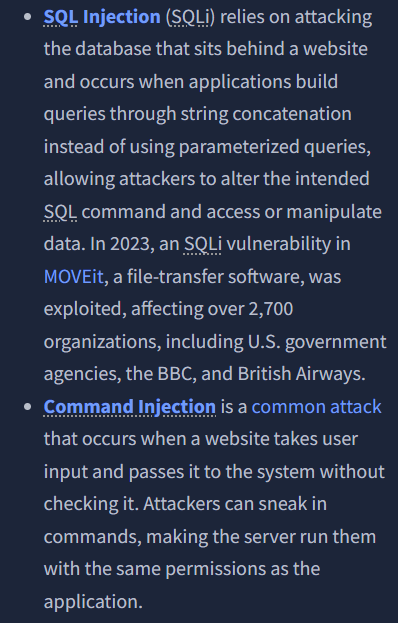
THM links to three rooms in this task: https://tryhackme.com/room/passwordattacks, https://tryhackme.com/room/sqlinjectionlm, and https://tryhackme.com/room/oscommandinjection/
For questions: “What class of attacks relies on exploiting vulnerabilities within web servers?” and “Which server-side attack lets attackers abuse forms to dump database contents?”

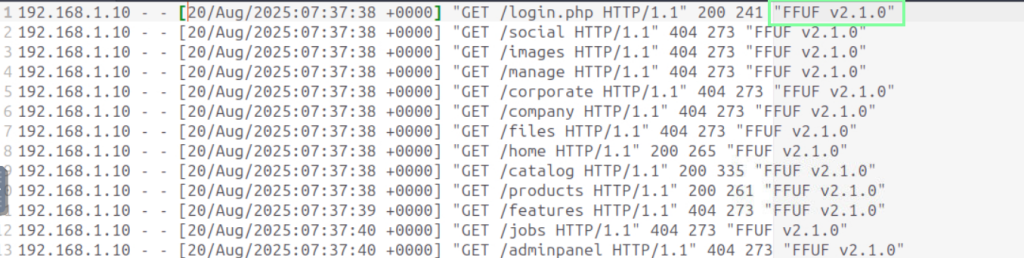
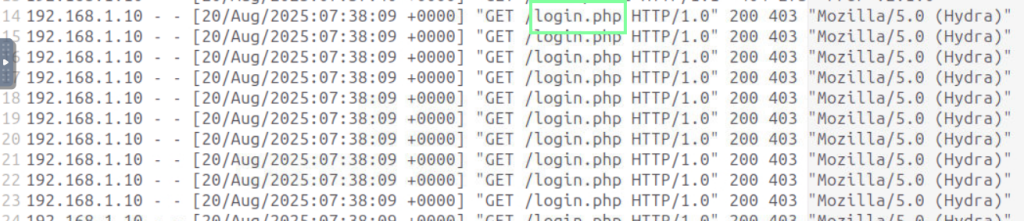
On to Task 4, Log-Based Detection! It appears that this room will be more technical than the previous tasks.

We are tasked with opening a log file from the desktop to obtain our answers.
“What is the attacker’s User-Agent while performing the directory fuzz?”
“What is the name of the page on which the attacker performs a brute-force attack?”
“What is the complete, decoded SQLi payload the attacker uses on the /changeusername.php form?”
CyberChef time! Usually, they have the offline version available in the VM, but I’m not seeing it. Go to cyberchef.org.

On to Task 5, Network-Based Detection!
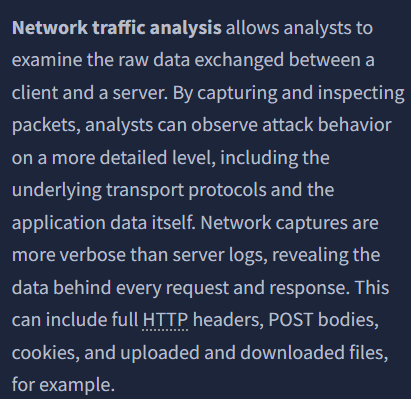
Navigate to the traffic.pcap file from the desktop, and it will load Wireshark.
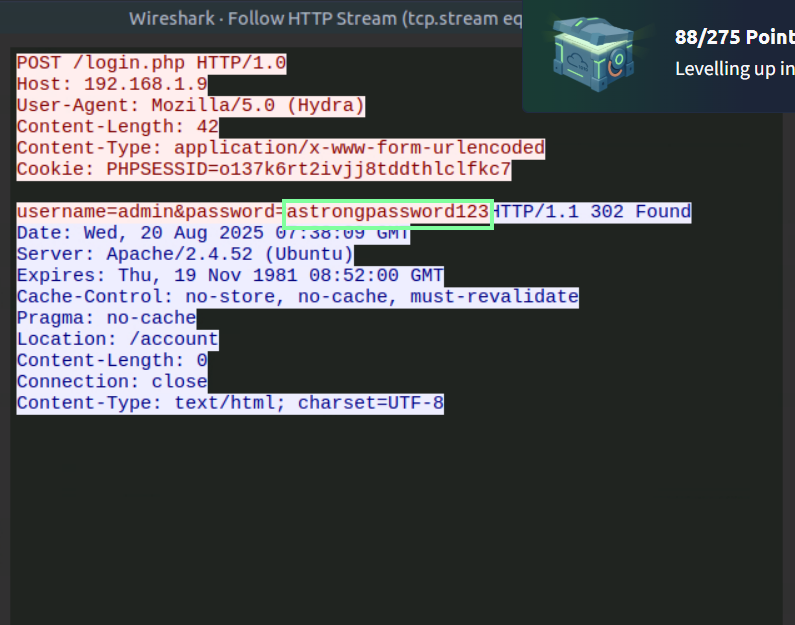
“What password does the attacker successfully identify in the brute-force attack?”
We can use this search filter to find successful logins(302).

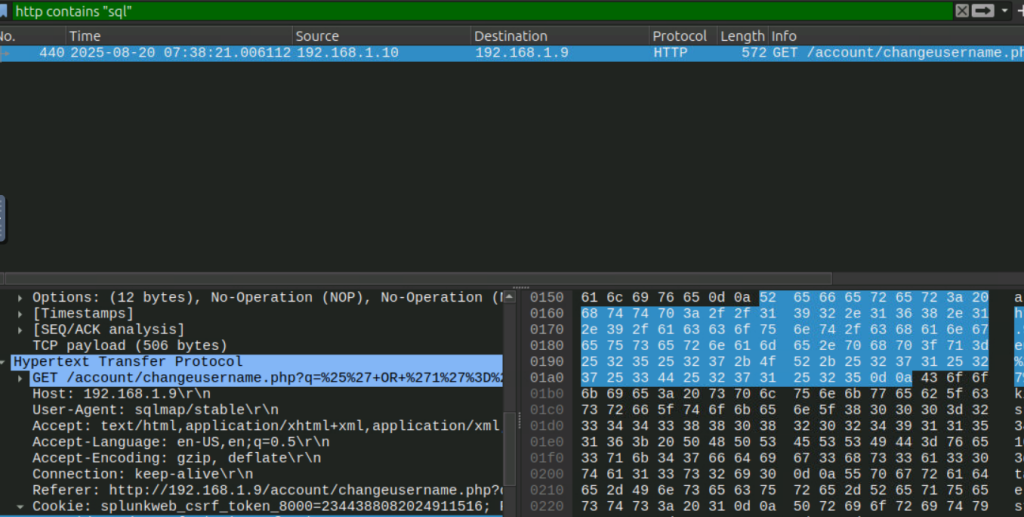
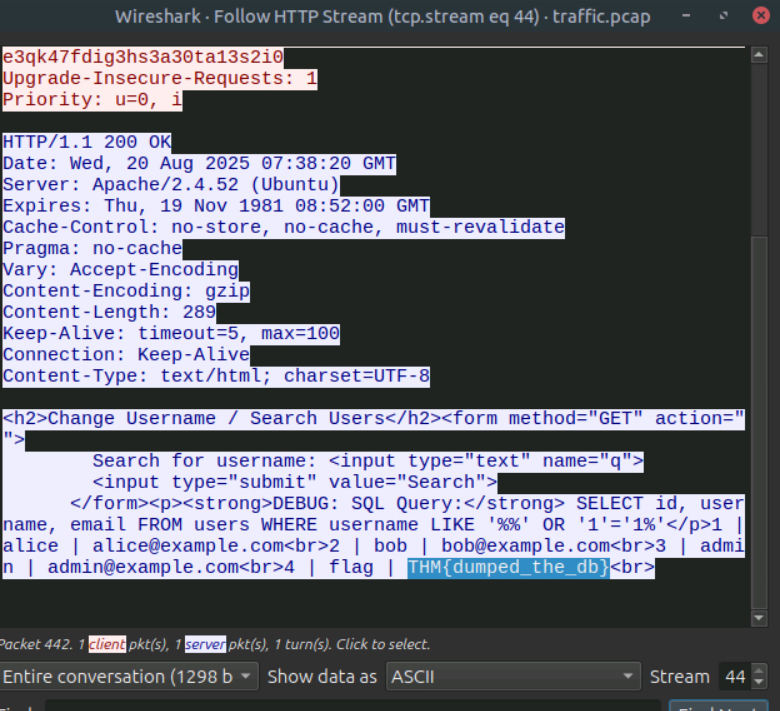
“What is the flag the attacker found in the database using SQLi?”
On to the last task, Web Application Firewall!
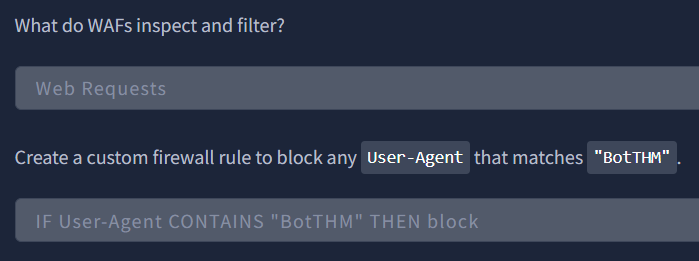
For the questions “What do WAFs inspect and filter? and “Create a custom firewall rule to block any User-Agent that matches "BotTHM".”