https://tryhackme.com/room/dataexfildetection
Created by: tryhackme, Dex01

There are two software we will be using in this lab: Wireshark and Splunk.

In Task 3, THM goes over Data exfiltration and various threat actors and their data exfiltration methods. Pet THM, “Data exfiltration is the unauthorized transfer of data from an organization to an external destination controlled by an adversary. It can be deliberate (insider) or via malware / compromised credentials.”



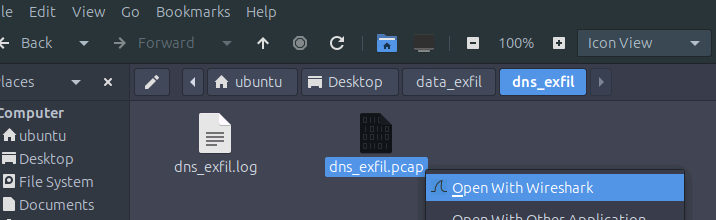
Going into task 4, THM has us go into Wireshark to investigate the dns pcap file.
“What is the suspicious domain receiving the DNS traffic?”
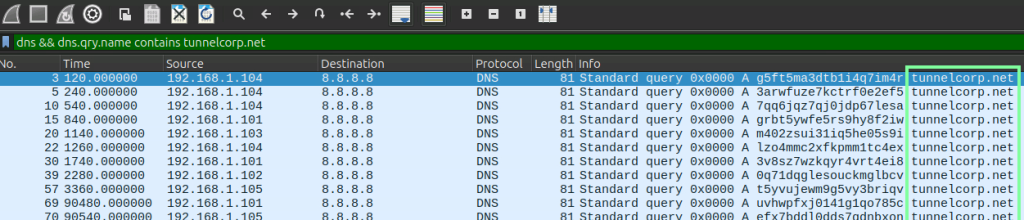
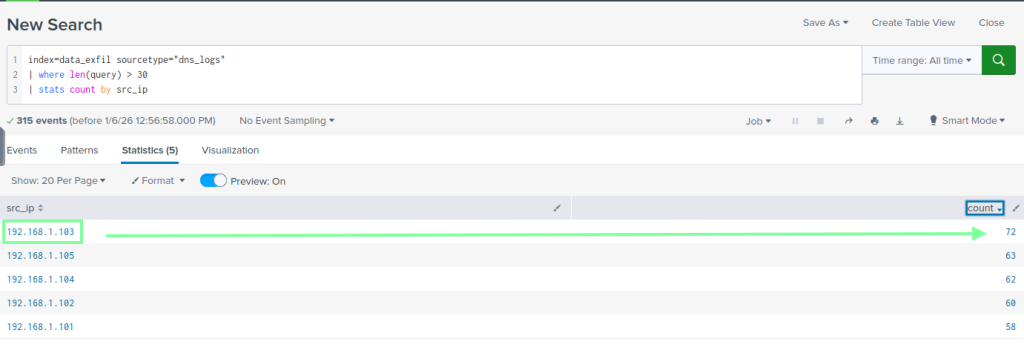
“How many suspicious traffic/logs related to dns tunneling were observed?”

“Which local IP sent the maximum number of suspicious requests?”
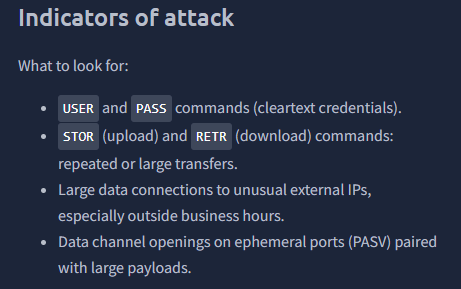
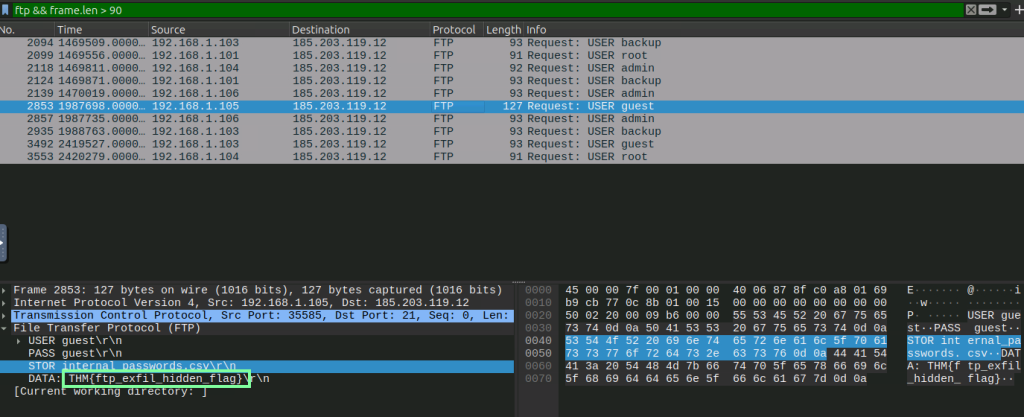
In the next task, we focus on ftp traffic and go back to Wireshark to analyze it.

“How many connections were observed from the guest account?” 5

“Apply the filter; what is the name of the customer-related file exfiltrated from the root account?”

“Which internal IP was found to be sending the largest payload to an external IP?”

“What is the flag hidden inside the ftp stream transferring the CSV file to the suspicious IP?”
Task 6 focuses on HTTP!

“Which internal compromised host was used to exfiltrate this sensitive data?”
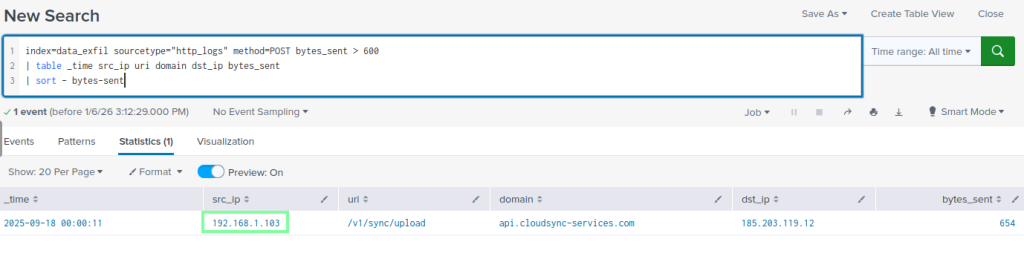
“What’s the flag hidden inside the exfiltrated data?”

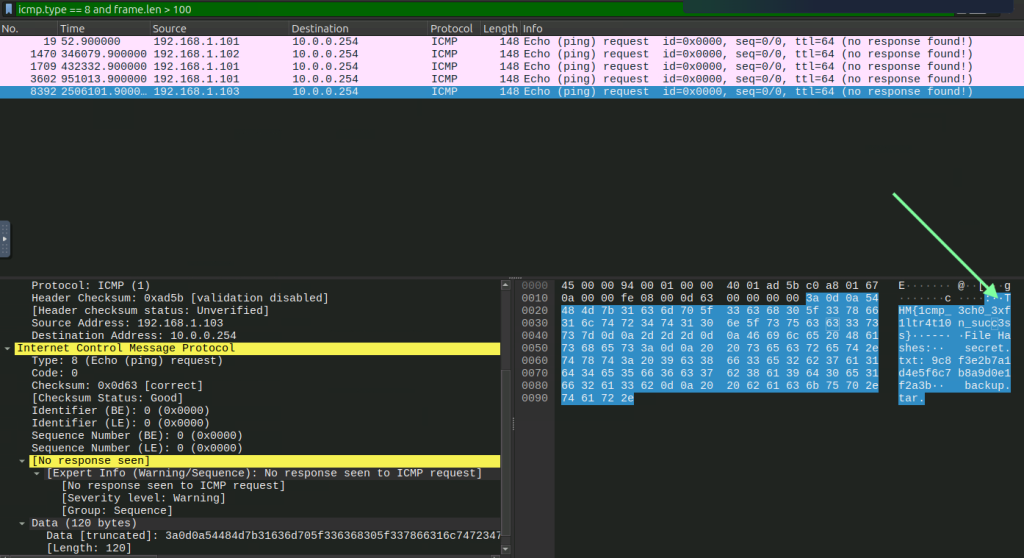
For our last task, we are focusing on ICMP!

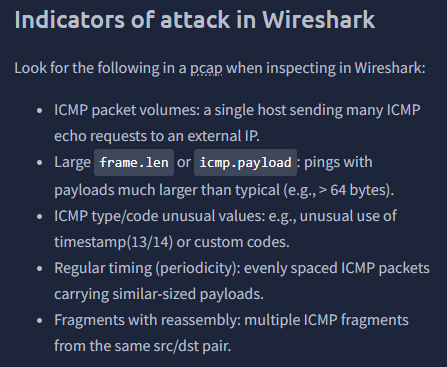
“What is the flag found in the exfiltrated data through ICMP?”
THM assists us with finding this flag. It’s still kind of hard to read, so what I did was copy the contents as base64, then used CyberChef to assist with getting it to read better.