https://tryhackme.com/room/networkdiscoverydetection
Created by: tryhackme


“What do attackers scan, other than IP addresses, ports, and OS versions, in order to identify vulnerabilities in a network?”
Services

I used this command to clean up things a little:
head log-session-2.csv | cut -d’,’ -f1,2,3,4,5,6,7,8,9,10,11
“Which file contains logs that showcase internal scanning activity?”

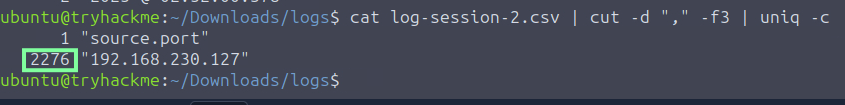
“How many log entries are present for the internal IP performing internal scanning activity?”
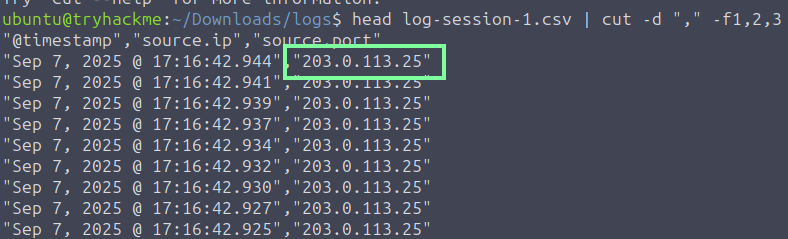
“What is the external IP address that is performing external scanning activity?”
In Task 4, THM breaks down Horizontal and Vertical scanning. Per Echo, “Horizontal scanning involves probing multiple hosts or IP addresses within a range, usually targeting the same port or service. It aims to identify vulnerabilities across different systems. Vertical scanning, on the other hand, focuses on a single host or IP address but examines multiple ports or services. This method is useful for discovering vulnerabilities in specific systems by exploring all potential entry points.”
This command gives us our next few answers.

“One of the log files contains evidence of a horizontal scan. Which IP range was scanned? Format X.X.X.X/X”

“In the same log file, there is one IP address on which a vertical scan is performed. Which IP address is this?”
“On one of the IP addresses, only a few ports are scanned which host common services. Which are the ports that are scanned on this IP address? Format: port1, port2, port3 in ascending order.”

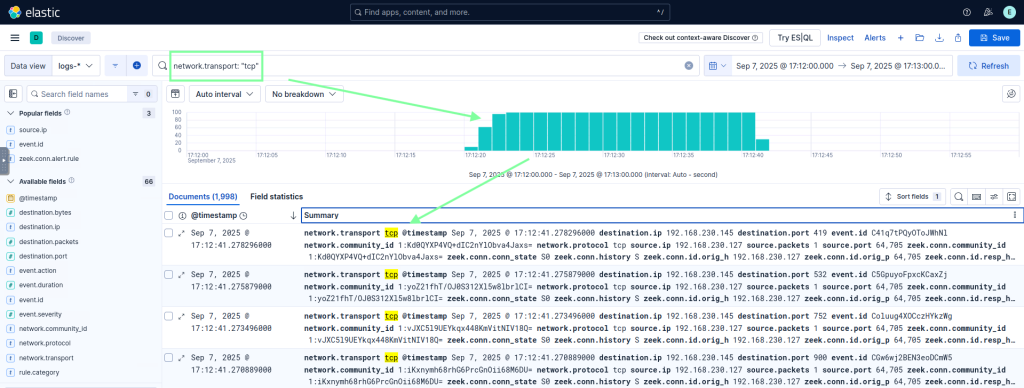
In Task 5, we get to use Elastic!
You can use various filters with Elastic. I used network.transport: “tcp” to locate the TCP scans. We can use this to obtain our next two answers
“Which source IP performs a ping sweep attack across a whole subnet?”
Source IP: 192.168.230.127
“The zeek.conn.conn_state value shows the connection state. Using the information provided by this value, identify the type of scan being performed by 203.0.113.25 against 192.168.230.145”
TCP SYN SCAN
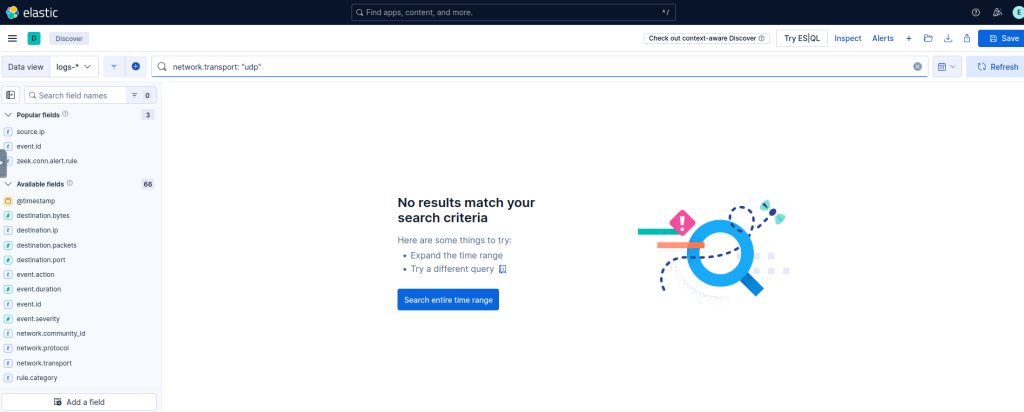
“Is there any UDP scanning attempt in the logs? Y/N” Nope, using network.tranpost: “udp” confirms this!