https://tryhackme.com/room/detecting-c2-with-rita-aoc2025-m9n2b5v8c1
Room created: tryhackme, Dex01, Gensane
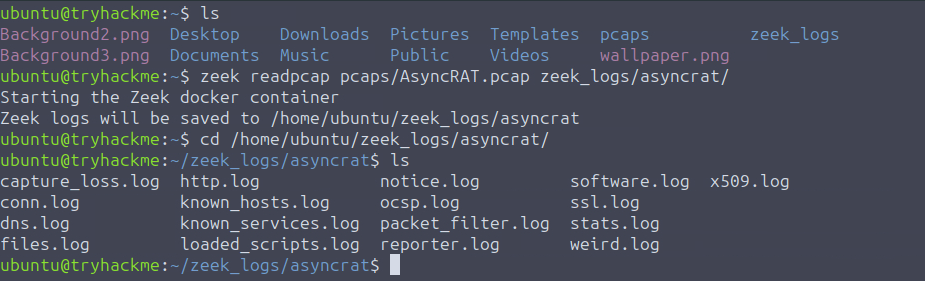
Per THM, “Packet capture (PCAP) is a networking practice involving the interception of data packets travelling over a network. Once the packets are captured, they can be stored by IT teams for further analysis. The inspection of these packets allows IT teams to identify issues and solve network problems affecting daily operations.
Zeek (formerly Bro) is the world’s leading platform for network security monitoring. Flexible, open source, and powered by defenders.”
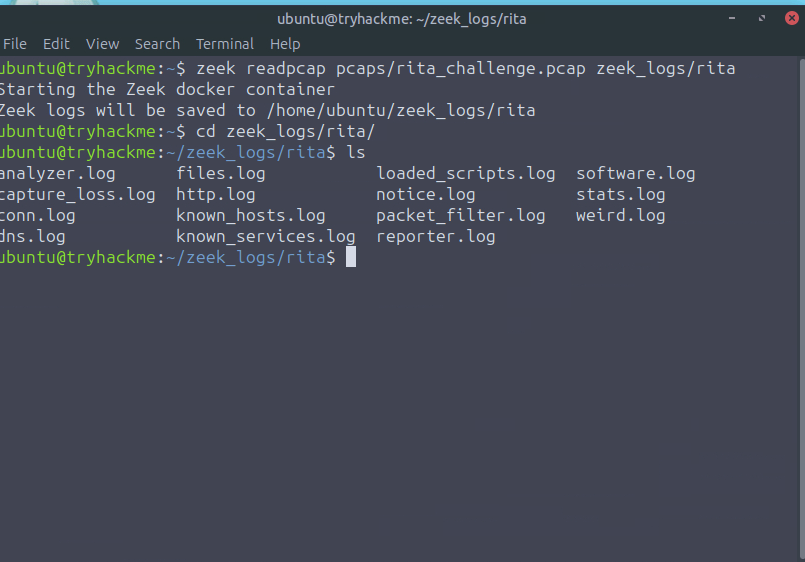
THM has us run a few commands to turn the pcap files into structured logs.
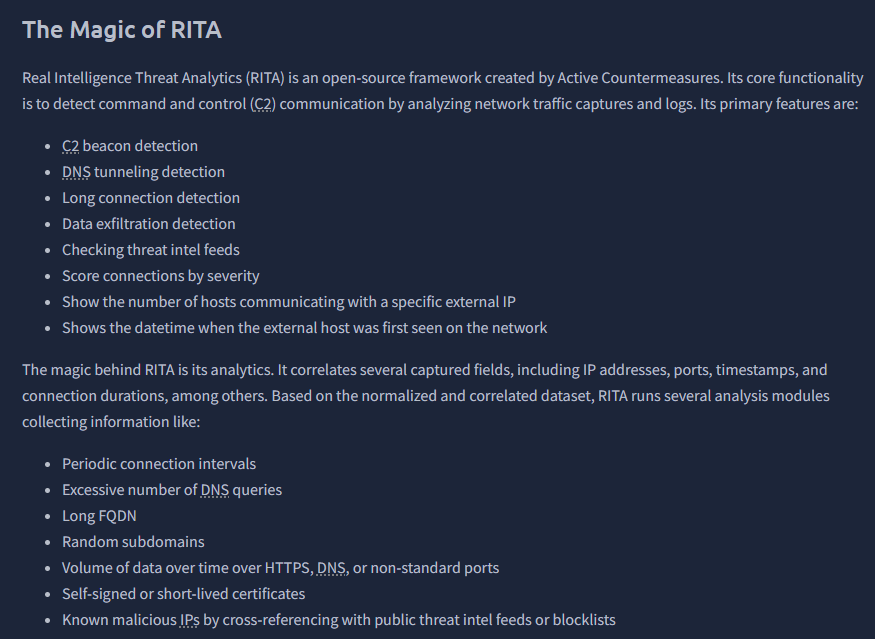
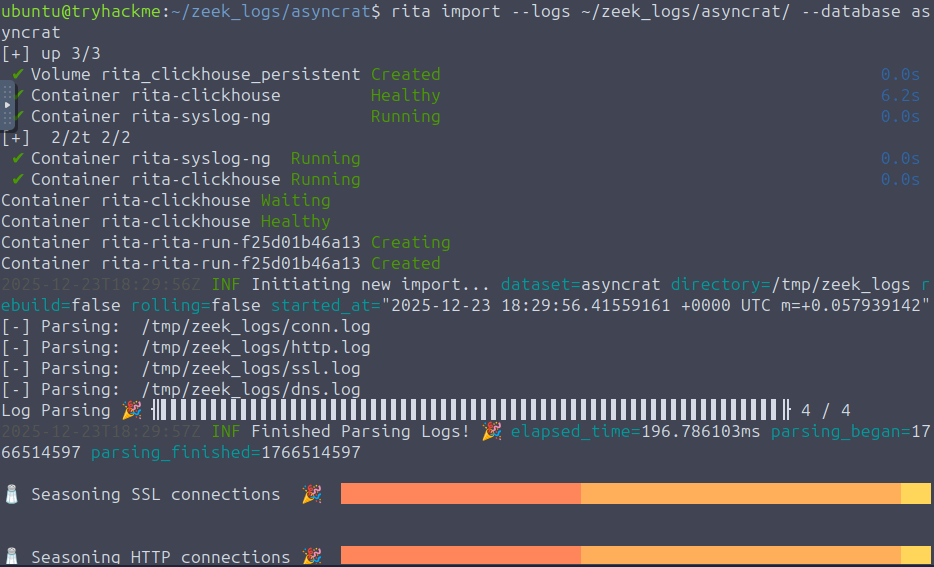
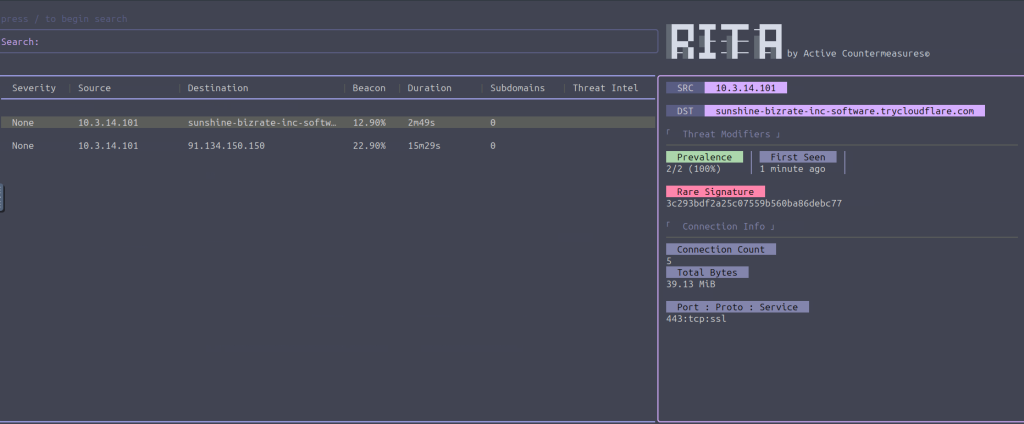
Next we are tasked with importing these logs into RITA.

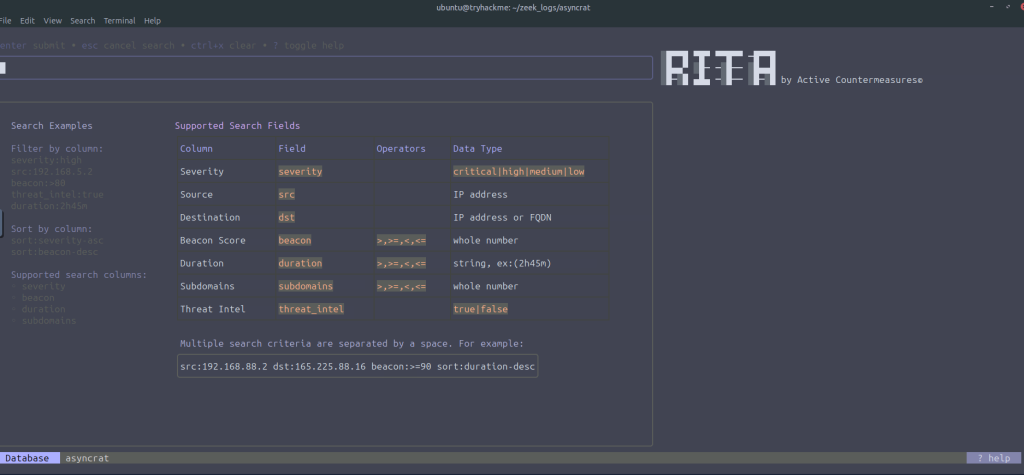
At this point, you will need to go full screen if you haven’t. I always like to keep split open as well so you can read and look at the VM at the same time if possible and are not required to do too much back in forth between tabs. THM instructs us to navigate the RITA utility with / to start a search and ? to look at various search fields.
Now we are tasked with looking at another pcap file: ~/pcaps/rita_challenge.pcap through the same steps as before. Remember: Don’t match everything with what THM had us do earlier; you will need to change a few things.

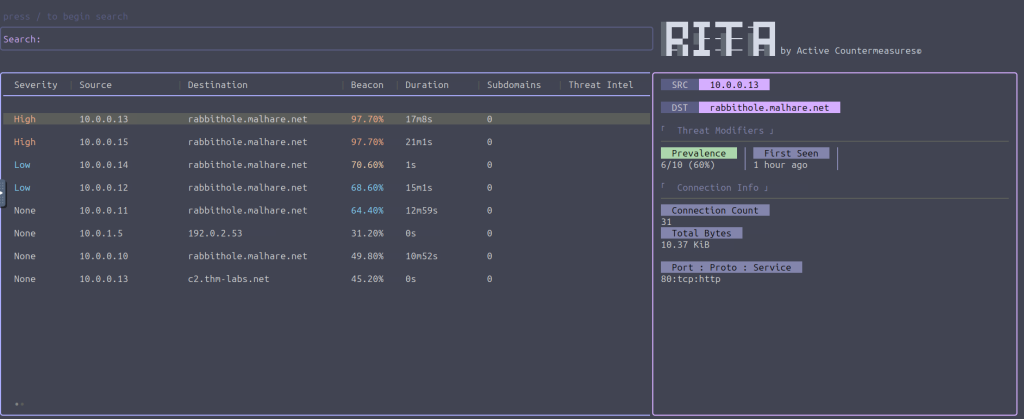
“How many hosts are communicating with malhare.net?”
“Which Threat Modifier tells us the number of hosts communicating to a certain destination?”
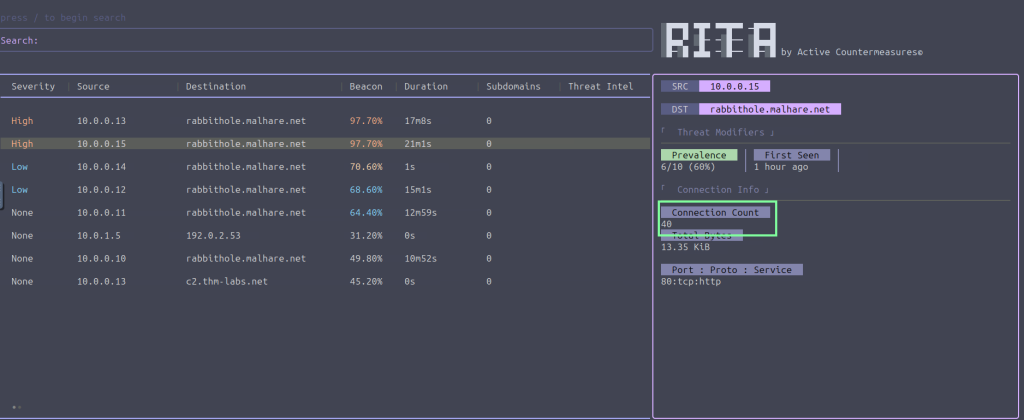
What is the highest number of connections to rabbithole.malhare.net?
“Which search filter would you use to search for all entries that communicate to rabbithole.malhare.net with a beacon score greater than 70% and sorted by connection duration (descending)?”
This question is not as bad as it seems if you go by the Search Examples within RITA.

‘Which port did the host 10.0.0.13 use to connect to rabbithole.malhare.net?’
